Access Control
Identify And Access Management Technique Mechanism Icon Information PDF
Persuade your audience using this Identify And Access Management Technique Mechanism Icon Information PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Identify, Access Management, Technique Mechanism. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Memcache Technology IT Limit Ip Access With Firewalls Pictures PDF
This slide explains how IP access is limited with firewalls, including setting up firewall rules to limit the computers. This is a memcache technology it limit ip access with firewalls pictures pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like limit ip access with firewalls. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Market Access With Arrow Icon Ppt PowerPoint Presentation File Smartart
Presenting this set of slides with name market access with arrow icon ppt powerpoint presentation file smartart. This is a one stage process. The stage in this process is market access with arrow icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
System Access To Management Ppt PowerPoint Presentation Topics
This is a system access to management ppt powerpoint presentation topics. This is a five stage process. The stages in this process are business, management, analysis, strategy, success, process.
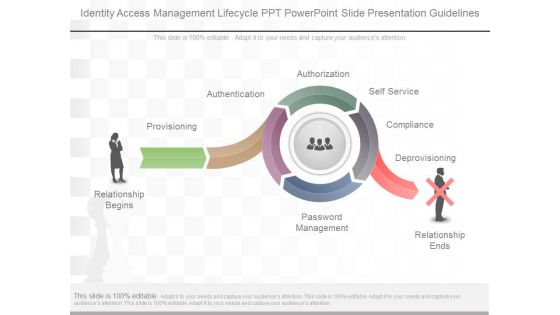
Identity Access Management Lifecycle Ppt Powerpoint Slide Presentation Guidelines
This is a identity access management lifecycle ppt powerpoint slide presentation guidelines. This is a five stage process. The stages in this process are relationship begins, provisioning, authentication, authorization, self service, compliance, deprovisioning, password management, relationship ends.
Zero Trust Network Access Architecture Overview Icons PDF
This slide gives an overview of zero trust network access architecture. The purpose of this slide is to showcase the ZTNA architecture and its benefits, covering granting safe and fast access, protecting reliable remote access, protecting sensitive data and apps, stopping insider threats, and so on. Retrieve professionally designed Zero Trust Network Access Architecture Overview Icons PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
Difference Identity Access Management Ppt PowerPoint Presentation Outline Introduction Cpb
Presenting this set of slides with name difference identity access management ppt powerpoint presentation outline introduction cpb. This is an editable Powerpoint five stages graphic that deals with topics like difference identity access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
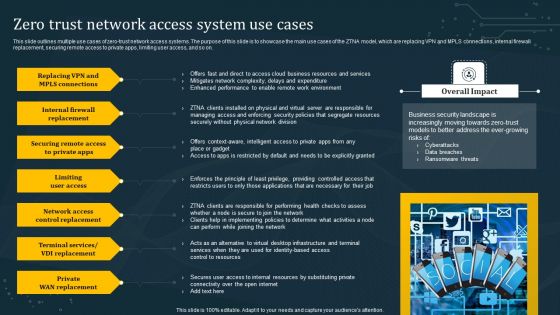
Zero Trust Network Access System Use Cases Summary PDF
This slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Boost your pitch with our creative Zero Trust Network Access System Use Cases Summary PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
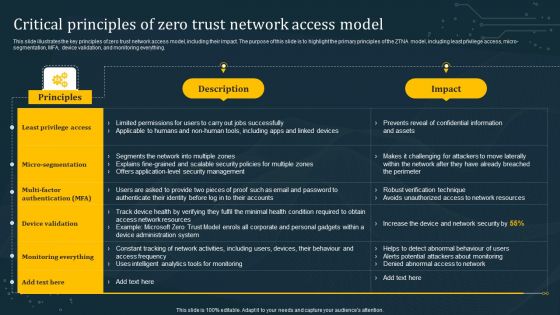
Critical Principles Of Zero Trust Network Access Model Graphics PDF
This slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Critical Principles Of Zero Trust Network Access Model Graphics PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Critical Principles Of Zero Trust Network Access Model Graphics PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
User Access Provisioning Process Ppt PowerPoint Presentation Portfolio Layouts Cpb
Presenting this set of slides with name user access provisioning process ppt powerpoint presentation portfolio layouts cpb. This is an editable Powerpoint four stages graphic that deals with topics like user access provisioning process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Access Review Process Ppt PowerPoint Presentation Show Graphic Images Cpb
Presenting this set of slides with name access review process ppt powerpoint presentation show graphic images cpb. This is an editable Powerpoint four stages graphic that deals with topics like access review process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Data Access Systems Ppt PowerPoint Presentation Layouts Gridlines Cpb
Presenting this set of slides with name data access systems ppt powerpoint presentation layouts gridlines cpb. This is an editable Powerpoint eight stages graphic that deals with topics like data access systems to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Ethical Hacking Phase 3 Gaining Access Ppt Pictures Vector PDF
This slide represents the gaining access phase of ethical hacking and how access can be gained through a phishing attack, man in the middle, brute force attack, and so on. This is a ethical hacking phase 3 gaining access ppt pictures vector pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like system, required. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Access Management Roles Responsibilities Ppt PowerPoint Presentation Ideas Example Cpb
Presenting this set of slides with name access management roles responsibilities ppt powerpoint presentation ideas example cpb. This is an editable Powerpoint three stages graphic that deals with topics like access management roles responsibilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Business Value Identity Access Management Ppt PowerPoint Presentation Summary Cpb
Presenting this set of slides with name business value identity access management ppt powerpoint presentation summary cpb. This is an editable Powerpoint three stages graphic that deals with topics like business value identity access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Access Management Ppt PowerPoint Presentation Pictures Layout Cpb Pdf
Presenting this set of slides with name secure access management ppt powerpoint presentation pictures layout cpb pdf. This is an editable Powerpoint five stages graphic that deals with topics like secure access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Parallel Computing Processing Introduction To Switched Memory Access Icons PDF
This slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Deliver and pitch your topic in the best possible manner with this Parallel Computing Processing Introduction To Switched Memory Access Icons PDF. Use them to share invaluable insights on Introduction To Switched, Memory Access and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Benefits Access Management Ppt PowerPoint Presentation Professional Smartart Cpb
Presenting this set of slides with name benefits access management ppt powerpoint presentation professional smartart cpb. This is an editable Powerpoint four stages graphic that deals with topics like benefits access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Identity Access Management Framework Ppt PowerPoint Presentation Portfolio Summary Cpb
Presenting this set of slides with name identity access management framework ppt powerpoint presentation portfolio summary cpb. This is an editable Powerpoint four stages graphic that deals with topics like identity access management framework to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Determine Identity And Access Management With 5G Contd Structure PDF
This slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver and pitch your topic in the best possible manner with this Determine Identity And Access Management With 5G Contd Structure PDF Use them to share invaluable insights on Mutual Authentication, Device Authentication, Traffic Encryption and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Determine Identity And Access Management With 5G Contd Information PDF
This slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver and pitch your topic in the best possible manner with this Determine Identity And Access Management With 5G Contd Information PDF. Use them to share invaluable insights on Application Traffic, Security, Network and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Quarterly Technology Implementation Roadmap Of Iris Access Regulations System Topics
We present our quarterly technology implementation roadmap of iris access regulations system topics. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched quarterly technology implementation roadmap of iris access regulations system topics in different formats like PDF, PNG, and JPG to smoothly execute your business plan.

Open Access Box With Gears Ppt PowerPoint Presentation Inspiration Demonstration
This is a open access box with gears ppt powerpoint presentation inspiration demonstration. This is a six stage process. The stages in this process are computer software, operating system, open source.

Open Access Collaborative Customizable Sharable Ppt PowerPoint Presentation File Backgrounds
This is a open access collaborative customizable sharable ppt powerpoint presentation file backgrounds. This is a seven stage process. The stages in this process are computer software, operating system, open source.

Addressing 5G Era Spectrum Bands Access And Pricing Clipart PDF
This slide provides details regarding various 5G era spectrum in terms of 5G spectrum bands, spectrum access and spectrum pricing. This is a Addressing 5G Era Spectrum Bands Access And Pricing Clipart PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Spectrum Bands, Spectrum Access, Spectrum Pricing. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Pillars Of Cloud Access Security Broker Ppt Show Background PDF
This slide represents the four major pillars of cloud access security broker. The purpose of this slide is to showcase the main pillars of implementing a cloud access security broker. The pillars include compliance, visibility, threat protection, and data security. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Pillars Of Cloud Access Security Broker Ppt Show Background PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Pillars Of Cloud Access Security Broker Ppt Show Background PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.

Application Of AI For Database Access Governance Summary PDF
This slide represents the applications of artificial intelligence systems for data access governance. The purpose of this slide is to demonstrate the AI application in secure data access. The use cases include threat detection and prediction, system configuration, adaptability, data interpretation, and predictive forecasting. Presenting Application Of AI For Database Access Governance Summary PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prediction, System Configuration, Adaptability. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

User Access Provisioning Process Ppt PowerPoint Presentation Example Cpb
Presenting this set of slides with name user access provisioning process ppt powerpoint presentation example cpb. This is an editable Powerpoint three stages graphic that deals with topics like user access provisioning process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Provisioning Lifecycle Ppt PowerPoint Presentation Show Cpb Pdf
Presenting this set of slides with name access provisioning lifecycle ppt powerpoint presentation show cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like access provisioning lifecycle to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Next Generation Access Ppt PowerPoint Presentation Portfolio Design Ideas Cpb
Presenting this set of slides with name next generation access ppt powerpoint presentation portfolio design ideas cpb. This is an editable Powerpoint six stages graphic that deals with topics like next generation access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Maximizing Access To Public Information Availability Rules PDF
This slide represents maximizing access to public data availability such as increase data availability, default, public data disclosure, decision making, data quality and data governance. Presenting maximizing access to public information availability rules pdf to dispense important information. This template comprises seven stages. It also presents valuable insights into the topics including data governance, data quality, decision making. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Database Access Security Measures For Businesses Portrait PDF
This slide represents the security measures for data access within an organization. This template aims to demonstrate secure data access techniques and their benefits. The components include workforce training, implementing a data-centric security plan, deploying a multi-factor authentication policy, etc. Pitch your topic with ease and precision using this Database Access Security Measures For Businesses Portrait PDF. This layout presents information on Methods, Benefits, Actions. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Secure Server Access Ppt PowerPoint Presentation Icon Show Cpb
Presenting this set of slides with name secure server access ppt powerpoint presentation icon show cpb. This is an editable Powerpoint four stages graphic that deals with topics like secure server access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Enterprise Access Governance Ppt PowerPoint Presentation Model Mockup Cpb
Presenting this set of slides with name enterprise access governance ppt powerpoint presentation model mockup cpb. This is an editable Powerpoint four stages graphic that deals with topics like enterprise access governance to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Data Access Ppt PowerPoint Presentation Inspiration Guidelines Cpb
Presenting this set of slides with name secure data access ppt powerpoint presentation inspiration guidelines cpb. This is an editable Powerpoint four stages graphic that deals with topics like secure data access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Individual Access Security Ppt PowerPoint Presentation Design Ideas Cpb
Presenting this set of slides with name individual access security ppt powerpoint presentation design ideas cpb. This is an editable Powerpoint three stages graphic that deals with topics like individual access security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Provider Access Ppt PowerPoint Presentation Summary Graphics Pictures Cpb Pdf
Presenting this set of slides with name provider access ppt powerpoint presentation summary graphics pictures cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like provider access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Sensitive Access Analysis Ppt PowerPoint Presentation Styles Influencers Cpb Pdf
Presenting this set of slides with name sensitive access analysis ppt powerpoint presentation styles influencers cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like sensitive access analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Database Replication Ppt PowerPoint Presentation Inspiration Show Cpb Pdf
Presenting this set of slides with name access database replication ppt powerpoint presentation inspiration show cpb pdf. This is an editable Powerpoint three stages graphic that deals with topics like access database replication to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Secure Access Lock Clipart Ppt PowerPoint Presentation Summary File Formats
This is a secure access lock clipart ppt powerpoint presentation summary file formats. This is a four stage process. The stages in this process are computer software, operating system, open source.

Secure Database Access Methods For Cloud Computing Formats PDF
This slide describes the various methods to access the data stored in a cloud environment securely. The purpose of this slide is to represent secure data access for cloud computing users. The methods include cloud-based access through a relational database management system, cloud-based data warehousing and a cloud data lake. Persuade your audience using this Secure Database Access Methods For Cloud Computing Formats PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cloud Data Lake, Data Warehousing, Cloud Service Provider. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Multiple Access Techniques Ppt PowerPoint Presentation Summary Portrait Cpb
Presenting this set of slides with name multiple access techniques ppt powerpoint presentation summary portrait cpb. This is an editable Powerpoint four stages graphic that deals with topics like multiple access techniques to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Market Access Strategy Example Powerpoint Slide Background Picture
This is a market access strategy example powerpoint slide background picture. This is a four stage process. The stages in this process are resource allocation, market assessment, economic modelling, product assessment.

Main Pillars Of Zero Network Trust Access Sample PDF
This slide outlines the critical pillars of the zero network trust access model. The purpose of this slide is to showcase the primary pillars of ZTNA, including users, devices, networks, infrastructure, applications, data, visibility and analytics, and orchestration and automation. Presenting this PowerPoint presentation, titled Main Pillars Of Zero Network Trust Access Sample PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Main Pillars Of Zero Network Trust Access Sample PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Main Pillars Of Zero Network Trust Access Sample PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Secure Access Service Edge Use Cases Ppt Outline Images PDF
This slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Explore a selection of the finest Secure Access Service Edge Use Cases Ppt Outline Images PDF here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Secure Access Service Edge Use Cases Ppt Outline Images PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Database Access Management Checklist For Businesses Formats PDF
This slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Showcasing this set of slides titled Database Access Management Checklist For Businesses Formats PDF. The topics addressed in these templates are Description, Status, Comments. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
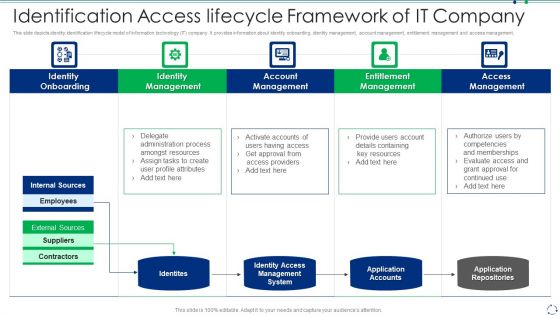
Identification Access Lifecycle Framework Of IT Company Portrait PDF
This slide depicts identity identification lifecycle model of information technology IT company. It provides information about identity onboarding, identity management, account management, entitlement management and access management.Persuade your audience using this identification access lifecycle framework of it company portrait pdf This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including identity onboarding, identity management, account management Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Key Pillars Of Identify And Access Management Technique Topics PDF
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Presenting Key Pillars Of Identify And Access Management Technique Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Provisioning Identities, Security Certification, Security Management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Training Program For Zero Trust Network Access Model Microsoft PDF
This slide outlines the training program for implementing the zero-trust network access model in the organization. The purpose of this slide is to highlight the training agenda, objectives, system requirements, mode of training and cost of the training. This Training Program For Zero Trust Network Access Model Microsoft PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Training Program For Zero Trust Network Access Model Microsoft PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
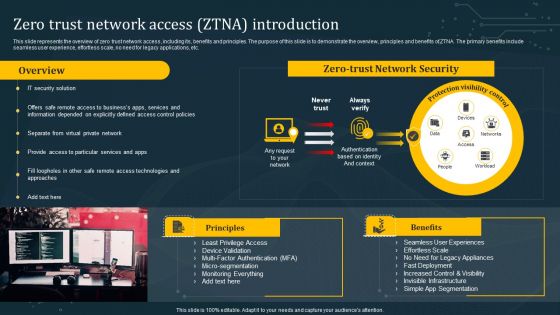
Zero Trust Network Access ZTNA Introduction Structure PDF
This slide represents the overview of zero trust network access, including its, benefits and principles. The purpose of this slide is to demonstrate the overview, principles and benefits of ZTNA. The primary benefits include seamless user experience, effortless scale, no need for legacy applications, etc. There are so many reasons you need a Zero Trust Network Access ZTNA Introduction Structure PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
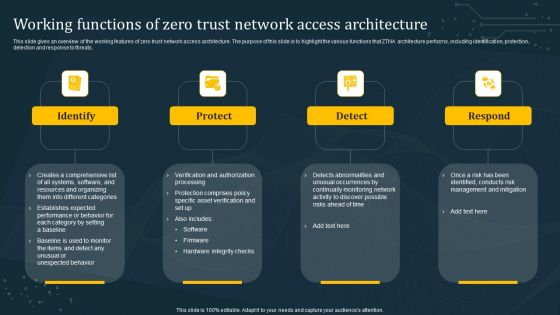
Working Functions Of Zero Trust Network Access Architecture Introduction PDF
This slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Explore a selection of the finest Working Functions Of Zero Trust Network Access Architecture Introduction PDF here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Working Functions Of Zero Trust Network Access Architecture Introduction PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Zero Trust Network Access User Flow Overview Mockup PDF
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Create an editable Zero Trust Network Access User Flow Overview Mockup PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Zero Trust Network Access User Flow Overview Mockup PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.

Zero Trust Network Access Vs Virtual Private Network Ideas PDF
This slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Zero Trust Network Access Vs Virtual Private Network Ideas PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Zero Trust Network Access Architecture Workflow Microsoft PDF
This slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Slidegeeks has constructed Zero Trust Network Access Architecture Workflow Microsoft PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

Ethical Hacking Phase 4 Maintaining Access Ppt Professional Grid PDF
This slide represents the maintaining access phase of ethical hacking and how ethical hackers take advantage of it to detect any malicious activities and prevent them. This is a ethical hacking phase 4 maintaining access ppt professional grid pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like system, information, determining. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
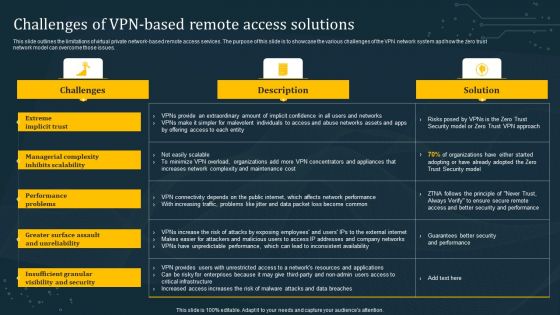
Challenges Of VPN Based Remote Access Solutions Template PDF
This slide outlines the limitations of virtual private network-based remote access services. The purpose of this slide is to showcase the various challenges of the VPN network system and how the zero trust network model can overcome those issues. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Challenges Of VPN Based Remote Access Solutions Template PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Challenges Of VPN Based Remote Access Solutions Template PDF today and make your presentation stand out from the rest
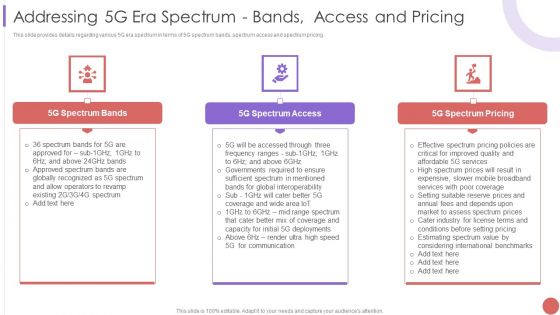
Addressing 5G Era Spectrum Bands Access And Pricing Download PDF
This slide provides details regarding various 5G era spectrum in terms of 5G spectrum bands, spectrum access and spectrum pricing. Presenting Addressing 5G Era Spectrum Bands Access And Pricing Download PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Approved Spectrum, Globally Recognized, Operators To Revamp In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Cloud Storage Access Methods Ppt Model Maker PDF
This slide depicts the cloud storage access methods such as web service APIs Application Programming Interface, file based APIs, block-based APIs, and other APIs. This is a cloud storage access methods ppt model maker pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like service, network internet, implement. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
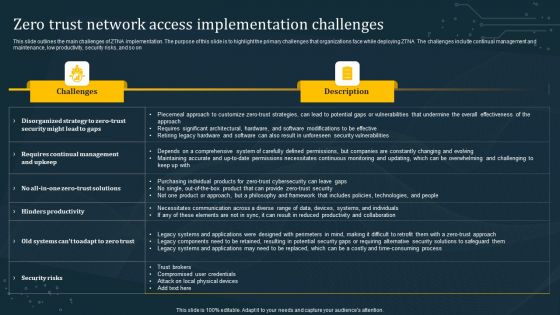
Zero Trust Network Access Implementation Challenges Rules PDF
This slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on. Presenting this PowerPoint presentation, titled Zero Trust Network Access Implementation Challenges Rules PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Zero Trust Network Access Implementation Challenges Rules PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Zero Trust Network Access Implementation Challenges Rules PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
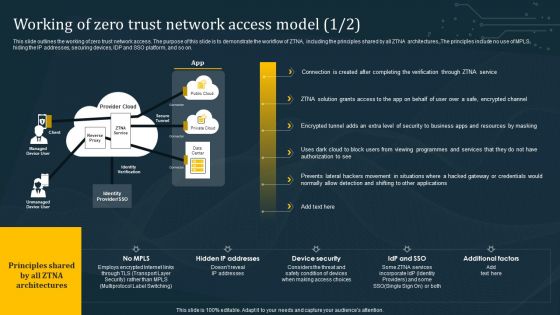
Working Of Zero Trust Network Access Model Summary PDF
This slide outlines the working of zero trust network access. The purpose of this slide is to demonstrate the workflow of ZTNA, including the principles shared by all ZTNA architectures. The principles include no use of MPLS, hiding the IP addresses, securing devices, IDP and SSO platform, and so on. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Working Of Zero Trust Network Access Model Summary PDF from Slidegeeks and deliver a wonderful presentation.

 Home
Home