Internet Security

Advancement Of Retail Store In Future Determine Different Technological Advancement Trends Brochure PDF
This slide provides information regarding different technological advancement trends in terms of diversification of payment options, shopping experience digitization, internet of things, data analytics, etc. This is a advancement of retail store in future determine different technological advancement trends brochure pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like diversification in payment methods, internet of things, data analytics, usage of social network services, shopping experience digitization. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Impeccable Information Technology Facility Client Standards Checklist Contd Clipart PDF
In order to maximize service delivery efficiencies, customer satisfaction, the firm standardised certain environmental qualifications for type of hardwares, softwares, operating systems. Presenting impeccable information technology facility client standards checklist contd clipart pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like internal network and internet, internet access, environment. In addition, this PPT design contains high-resolution images, graphics, etc, that are easily editable and available for immediate download.

Tools For Strategic Business Conversational Abilities Enhancement Template PDF
The following slide highlights skills enhancement using strategic communication tools to provide and receive feedback, customer solicitation, occasional updates, sharing ideas etc. It includes tools such as email, social networking websites, instant messages, web conferences and voice over internet etc. Persuade your audience using this Tools For Strategic Business Conversational Abilities Enhancement Template PDF. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including Web Conferences, Instant Messengers, Voice Over Internet Protocol. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
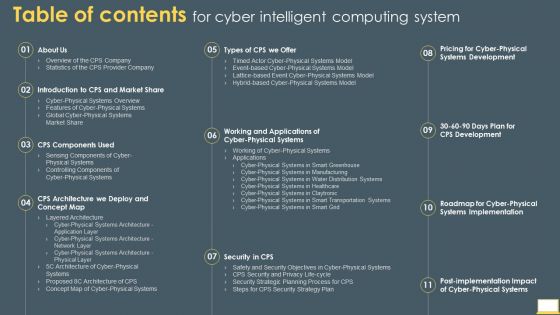
Table Of Contents For Cyber Intelligent Computing System Infographics PDF
Deliver an awe inspiring pitch with this creative Table Of Contents For Cyber Intelligent Computing System Infographics PDF bundle. Topics like Systems Development, Systems Implementation, Security Strategy Plan can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
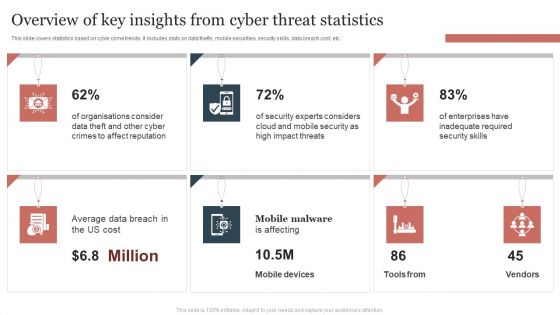
Overview Of Key Insights From Cyber Threat Statistics Themes PDF
This slide covers statistics based on cyber crime trends. It includes stats on data thefts, mobile securities, security skills, data breach cost, etc. Showcasing this set of slides titled Overview Of Key Insights From Cyber Threat Statistics Themes PDF. The topics addressed in these templates are Overview Of Key Insights, Cyber Threat Statistics . All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Top Challenges Analysis For Iot Sample Ppt Sample Presentations
This is a top challenges analysis for iot sample ppt sample presentations. This is a eight stage process. The stages in this process are byod and user dept devices, 3rd party data requests, compliance requirements, security threats, external attacks, access management, data privacy, other.
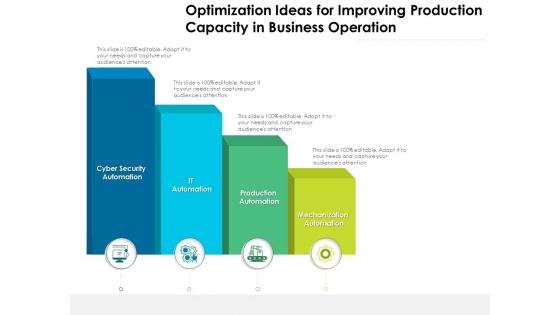
Optimization Ideas For Improving Production Capacity In Business Operation Ppt PowerPoint Presentation Outline Visual Aids PDF
Presenting this set of slides with name optimization ideas for improving production capacity in business operation ppt powerpoint presentation outline visual aids pdf. This is a four stage process. The stages in this process are mechanization automation, production automation, it automation, cyber security automation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Organization Reinvention Company Spending On New Technologies Microsoft PDF
This graph covers the companys investments in new technologies to accelerate growth and productivity. Deliver an awe inspiring pitch with this creative Organization Reinvention Company Spending On New Technologies Microsoft PDF bundle. Topics like Social, Technologies, Cyber Security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
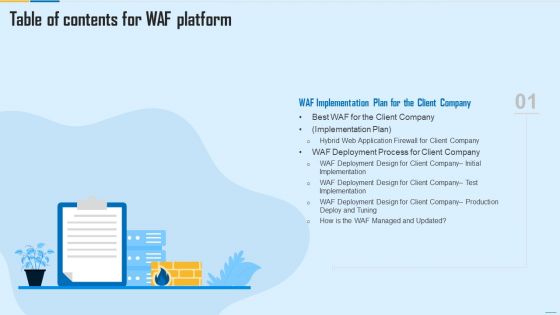
Table Of Contents For WAF Platform Plan Guidelines PDF
Deliver an awe inspiring pitch with this creative Table Of Contents For WAF Platform Plan Guidelines PDF bundle. Topics like Web Application Firewall, Centralized Management System, Firewall Security Models can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Networking Device Icon Circle Arrow Ppt PowerPoint Presentation Complete Deck
Presenting this set of slides with name networking device icon circle arrow ppt powerpoint presentation complete deck. The topics discussed in these slides are technology, router device, circle, arrow, security shield. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
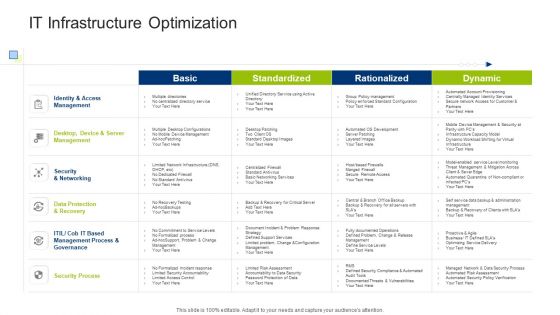
Infrastructure Building Administration IT Infrastructure Optimization Formats PDF
Deliver and pitch your topic in the best possible manner with this infrastructure building administration it infrastructure optimization formats pdf. Use them to share invaluable insights on identity and access management, security and networking, data protection and recovery and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

SIEM Services How SIEM Works Ppt Microsoft PDF
Deliver an awe inspiring pitch with this creative siem services how siem works ppt microsoft pdf bundle. Topics like network device, operating systems, security device, vulnerability and threats can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
IT Management Elements Shown Through Three Gears Ppt PowerPoint Presentation Icon Files PDF
Presenting it management elements shown through three gears ppt powerpoint presentation icon files pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including incident management, security management, network management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
IT Management Elements Shown Through Four Gears Ppt PowerPoint Presentation Gallery Clipart Images PDF
Presenting it management elements shown through four gears ppt powerpoint presentation gallery clipart images pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including incident management, security management, network management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
IT Management Elements Shown Through Five Gears Ppt PowerPoint Presentation File Portfolio PDF
Presenting it management elements shown through five gears ppt powerpoint presentation file portfolio pdf to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including incident management, security management, network management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
IT Management Elements Shown Through Six Gears Ppt PowerPoint Presentation Gallery Graphics PDF
Presenting it management elements shown through six gears ppt powerpoint presentation gallery graphics pdf to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including incident management, security management, network management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

IT Management Elements Shown Through Seven Gears Ppt PowerPoint Presentation Gallery Example PDF
Presenting it management elements shown through seven gears ppt powerpoint presentation gallery example pdf to dispense important information. This template comprises seven stages. It also presents valuable insights into the topics including incident management, security management, network management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
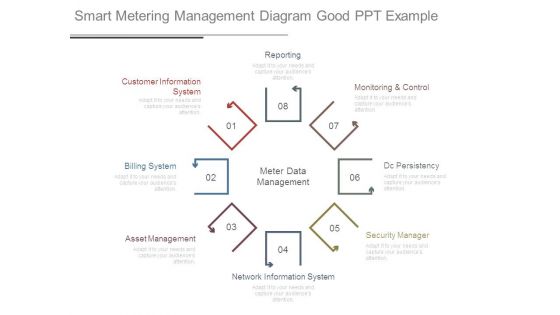
Smart Metering Management Diagram Good Ppt Example
This is a smart metering management diagram good ppt example. This is a eight stage process. The stages in this process are reporting, customer information system, billing system, asset management, network information system, security manager, dc persistency, monitoring and control, meter data management.
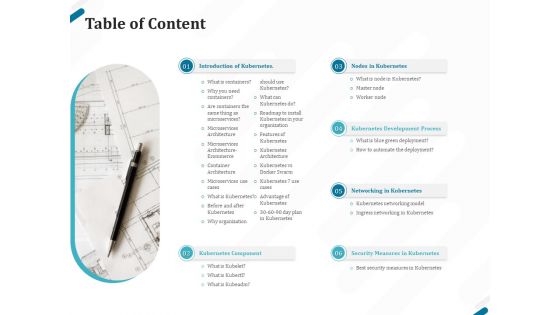
Kubernetes Containers Architecture Overview Table Of Content Ppt Summary Layout Ideas PDF
Presenting this set of slides with name kubernetes containers architecture overview table of content ppt summary layout ideas pdf. This is a six stage process. The stages in this process are introduction kubernetes, kubernetes component, nodes kubernetes, kubernetes development process, networking kubernetes, security measures kubernetes. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
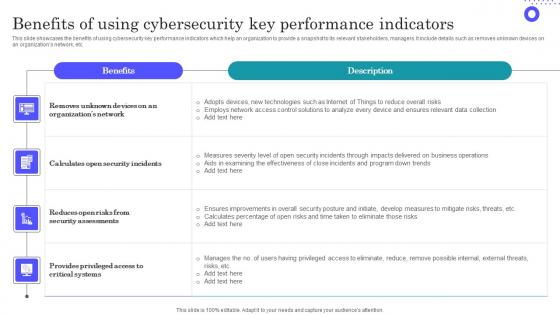
Benefits Of Using Cybersecurity Key Performance Indicators Slides Pdf
Showcasing this set of slides titled Benefits Of Using Cybersecurity Key Performance Indicators Slides Pdf The topics addressed in these templates are Organizations Network, Security Assessments, Provides Privileged All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
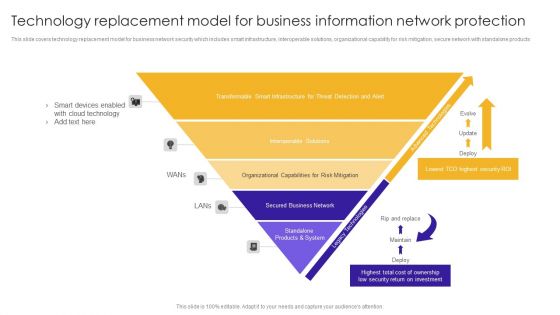
Technology Replacement Model For Business Information Network Protection Structure PDF
This slide covers technology replacement model for business network security which includes smart infrastructure, interoperable solutions, organizational capability for risk mitigation, secure network with standalone products.Showcasing this set of slides titled Technology Replacement Model For Business Information Network Protection Structure PDF. The topics addressed in these templates are Smart Devices, Cloud Technology, Transformable Smart. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Naas Integrated Solution IT Virtual Private Network VPN Model Overview Designs PDF
This slide represents the overview of the virtual private network, including its benefits, such as protecting customer information from hackers, preventing internet service provider companies and websites from selling customer data, and so on. Deliver an awe inspiring pitch with this creative Naas Integrated Solution IT Virtual Private Network VPN Model Overview Designs PDF bundle. Topics like Secured Communication, Business, Information can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
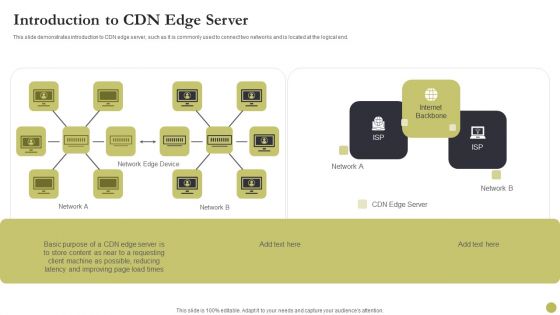
Content Delivery Network Edge Server Introduction To CDN Edge Server Designs PDF
Deliver an awe inspiring pitch with this creative Content Delivery Network Edge Server Introduction To CDN Edge Server Designs PDF bundle. Topics like Network, Internet Backbone can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
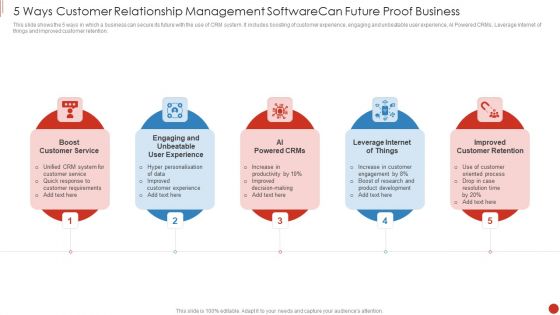
5 Ways Customer Relationship Management Software Can Future Proof Business Mockup PDF
This slide shows the 5 ways in which a business can secure its future with the use of CRM system. It includes boosting of customer experience, engaging and unbeatable user experience, AI Powered CRMs, Leverage internet of things and improved customer retention. Presenting 5 Ways Customer Relationship Management Software Can Future Proof Business Mockup PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Customer Service, Engaging Unbeatable, Powered Crms This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Find The Point Of Success PowerPoint Templates Ppt Backgrounds For Slides 0613
Drive confidently over all the bumps. Our Find The Point Of Success PowerPoint Templates PPT Backgrounds For Slides will absorb the shocks. Take a drive into unknown territory. Our Internet PowerPoint Templates will provide the co-ordinates. Drive out of difficulty with our Technology PowerPoint Templates. They will steer you to safety.

Website Programming IT What HTTP And HTTPS Means Ppt PowerPoint Presentation File Model PDF
This slide depicts the meaning of HTTP and HTTPS, how data is transferred over the internet via both protocols, and how HTTPS is safe than HTTP. Deliver and pitch your topic in the best possible manner with this website programming it what http and https means ppt powerpoint presentation file model pdf. Use them to share invaluable insights on insecure connection, encrypted connection, secure http and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Iot Logistics Comprehensive Training Program Ideas PDF
This slide showcases internet of things IoT comprehensive training program. It provides details such as modules, trainer, time, outcome, worker performance, productivity, IoT architecture, big data, analytics, warehouse IoT, testing, support, etc. Deliver and pitch your topic in the best possible manner with this Iot Logistics Comprehensive Training Program Ideas PDF. Use them to share invaluable insights on Transportation Management, Security, Data Management and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Analyzing Impact Of Blockchain Iot On Major Kpis Icons PDF
This slide showcases impact analysis of blockchain internet of things IoT on key performance indicators KPIs. It provides information about efficiency, security, risk, costs, business models, revenue resources, etc. Deliver an awe inspiring pitch with this creative Analyzing Impact Of Blockchain Iot On Major Kpis Icons PDF bundle. Topics like Blockchain Integration, Business Model, Revenue Sources can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Analyzing Impact Of Blockchain Iot On Major Kpis Formats PDF
This slide showcases impact analysis of blockchain internet of things IoT on key performance indicators KPIs. It provides information about efficiency, security, risk, costs, business models, revenue resources, etc. Deliver an awe inspiring pitch with this creative Analyzing Impact Of Blockchain Iot On Major Kpis Formats PDF bundle. Topics like Operational Efficiency, Information, Existing System can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Infographics Option Banner With Umbrella Powerpoint Templates
Who doesn?t want to have a secure life? Be it financial security, safety of your child or safe environment at home and at work place. Well we hope for that but we can definitely save you from making ugly PowerPoint presentations. Above is the slide which is of umbrella with four options and along with it are four icons. This slide is one of our most downloaded PowerPoint slides and can be used to depict safety and security of any kind. The umbrella here can be used to indicate the safety, security, protection so you can choose this slide to show why it is safe to be associated with your company, or with your business, with your school, how your money is safe and secured in your bank or how it is safe if you pay online and much more. It is a multipurpose slide and can easily be modified as you want. Choose this slide to make your PowerPoint presentation look even more fantastic.
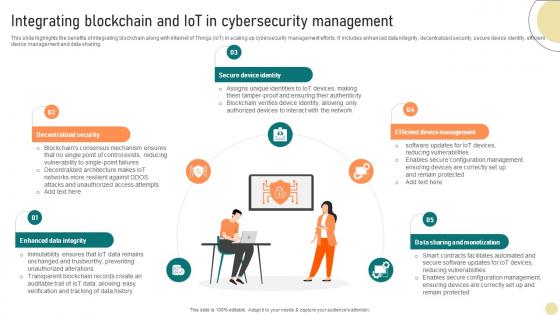
Visionary Guide To Blockchain Technologys Integrating Blockchain And IoT BCT SS V
This slide highlights the benefits of integrating blockchain along with Internet of Things IoT in scaling up cybersecurity management efforts. It includes enhanced data integrity, decentralized security, secure device identity, efficient device management and data sharing. Find highly impressive Visionary Guide To Blockchain Technologys Integrating Blockchain And IoT BCT SS V on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Visionary Guide To Blockchain Technologys Integrating Blockchain And IoT BCT SS V for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now

Comprehensive Look At Blockchain Technologys Integrating Blockchain And IoT BCT SS V
This slide highlights the benefits of integrating blockchain along with Internet of Things IoT in scaling up cybersecurity management efforts. It includes enhanced data integrity, decentralized security, secure device identity, efficient device management and data sharing. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Comprehensive Look At Blockchain Technologys Integrating Blockchain And IoT BCT SS V. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Comprehensive Look At Blockchain Technologys Integrating Blockchain And IoT BCT SS V today and make your presentation stand out from the rest

Web Consulting Business Cybersecurity Issues Overview And Key Statistics
Mentioned slide provides introduction about cyber security issues. It includes key elements such as description, types of security issue, key facts, and negative impact on business. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Web Consulting Business Cybersecurity Issues Overview And Key Statistics to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.

Enhancing Cyber Safety With Vulnerability Administration SIEM Integrations Inspiration PDF
This is a enhancing cyber safety with vulnerability administration siem integrations inspiration pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like security events, network logs, applications and devices, it infrastructure. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Exploitation IT Budget For IT Spending By The Company Professional PDF
This slide represents the IT spending budget for the advancements and cyber security policy changes that the organization will implement in the coming years. Deliver an awe inspiring pitch with this creative cyber exploitation it budget for it spending by the company professional pdf bundle. Topics like mobile devices, it peripherals, it services, servers, storage and network can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
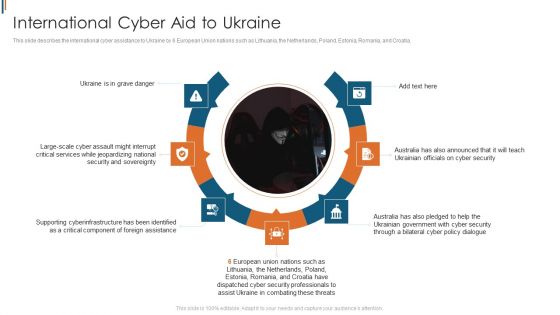
Ukraine Cyberwarfare International Cyber Aid To Ukraine Brochure Pdf
This slide describes the international cyber assistance to Ukraine by 6 European Union nations such as Lithuania, the Netherlands, Poland, Estonia, Romania, and Croatia. This is a ukraine cyberwarfare international cyber aid to ukraine brochure pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like ukraine is in grave danger, australia has also announced that it will teach ukrainian officials on cyber security, australia has also pledged to help the ukrainian government with cyber security through a bilateral cyber policy dialogue. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Zero Trust Network Access Comparison Between Zero Trust Model SDP And VPN
This slide represents the comparison between the zero trust security model, software-defined perimeter, and virtual private network. The purpose of this slide is to showcase the difference as well as the relationship between three security technologies such as zero trust, SDP and VPN. Welcome to our selection of the Zero Trust Network Access Comparison Between Zero Trust Model SDP And VPN. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100Percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today.

Zero Trust Model Zero Trust Network Access User Flow Overview
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Retrieve professionally designed Zero Trust Model Zero Trust Network Access User Flow Overview to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.

Enterprise Cyber Risk Management Dashboard Sample PDF
This slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. There are so many reasons you need a Enterprise Cyber Risk Management Dashboard Sample PDF. The first reason is you cannot spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
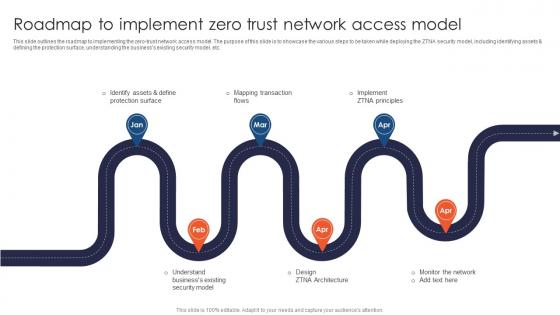
Zero Trust Network Access Roadmap To Implement Zero Trust Network Access Model
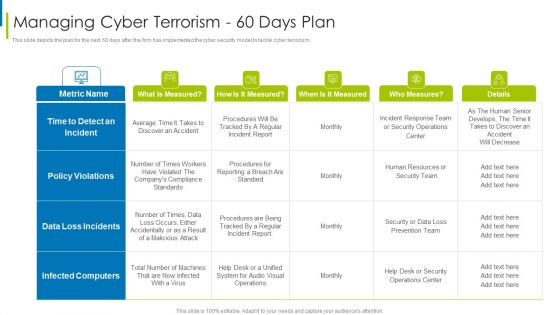
Cyber Terrorism Assault Managing Cyber Terrorism 60 Days Plan Clipart PDF
This slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault managing cyber terrorism 60 days plan clipart pdf Use them to share invaluable insights on time to detect an incident, data loss incidents, infected computers and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Global Cyber Terrorism Incidents On The Rise IT Managing Cyber Terrorism 90 Days Plan Structure PDF
This slide demonstrates the cyber security models 90-day strategy in an enterprise, as well as training compliance and communication strategies. Deliver and pitch your topic in the best possible manner with this global cyber terrorism incidents on the rise it managing cyber terrorism 90 days plan structure pdf. Use them to share invaluable insights on training completion, communication methods, policy sign off and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
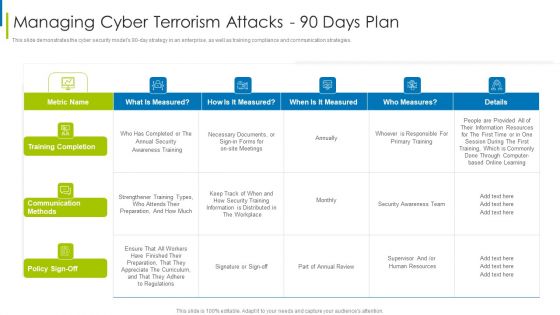
Cyber Terrorism Assault Managing Cyber Terrorism Attacks 90 Days Plan Formats PDF
This slide demonstrates the cyber security models 90 to day strategy in an enterprise, as well as training compliance and communication strategies.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault managing cyber terrorism attacks 90 days plan formats pdf Use them to share invaluable insights on training completion, communication methods, information is distributed and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Cyber Intelligent Computing System Sensing Components Of Cyber Physical Systems Elements PDF
This slide depicts the sensing components of cyber security systems, including sensors, aggregators, actuators, and their operations and position on the architecture. Deliver an awe inspiring pitch with this creative Cyber Intelligent Computing System Sensing Components Of Cyber Physical Systems Elements PDF bundle. Topics like Information Acquired, Analyze, Environment can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
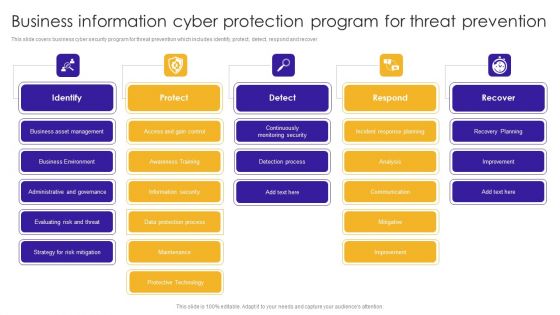
Business Information Cyber Protection Program For Threat Prevention Background PDF
This slide covers business cyber security program for threat prevention which includes identify, protect, detect, respond and recover.Showcasing this set of slides titled Business Information Cyber Protection Program For Threat Prevention Background PDF. The topics addressed in these templates are Business Environment, Administrative Governance, Evaluating Risk. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
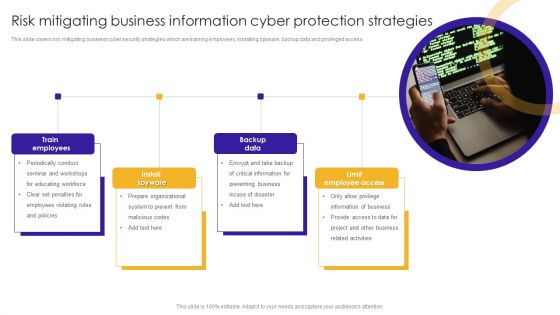
Risk Mitigating Business Information Cyber Protection Strategies Themes PDF
This slide covers risk mitigating business cyber security strategies which are training employees, installing spyware, backup data and privileged access.Presenting Risk Mitigating Business Information Cyber Protection Strategies Themes PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Train Employees, Information Business, Related Activities. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Reshaping Business In Digital Company Spending On New Technologies Clipart PDF
This graph covers the companys investments in new technologies to accelerate growth and productivity. Deliver an awe inspiring pitch with this creative Reshaping Business In Digital Company Spending On New Technologies Clipart PDF bundle. Topics like Corporate Spending, New Technologies, Cyber Security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
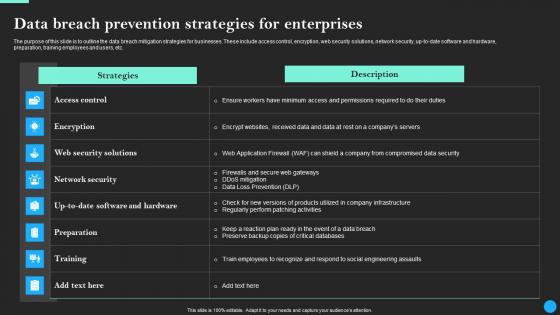
Data Breach Prevention Strategies For Enterprises Data Breach Prevention Slides Pdf
The purpose of this slide is to outline the data breach mitigation strategies for businesses. These include access control, encryption, web security solutions, network security, up-to-date software and hardware, preparation, training employees and users, etc. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Data Breach Prevention Strategies For Enterprises Data Breach Prevention Slides Pdf was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Data Breach Prevention Strategies For Enterprises Data Breach Prevention Slides Pdf
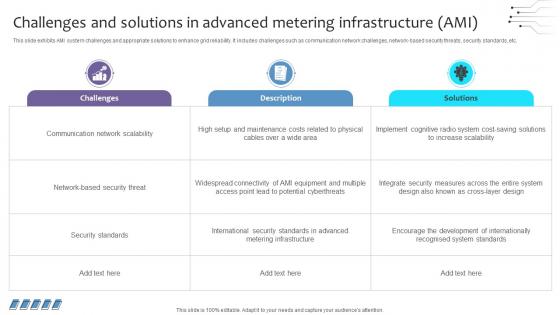
Empowering The Future Challenges And Solutions In Advanced Metering Infrastructure IoT SS V
This slide exhibits AMI system challenges and appropriate solutions to enhance grid reliability. It includes challenges such as communication network challenges, network-based security threats, security standards, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Empowering The Future Challenges And Solutions In Advanced Metering Infrastructure IoT SS V. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Empowering The Future Challenges And Solutions In Advanced Metering Infrastructure IoT SS V today and make your presentation stand out from the rest
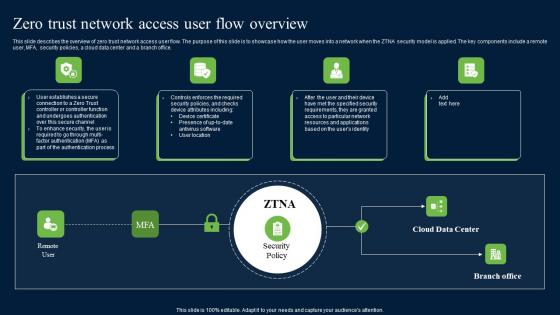
Zero Trust Network Access User Flow Overview Download Pdf
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Slidegeeks is here to make your presentations a breeze with Zero Trust Network Access User Flow Overview Download Pdf With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first

Zero Trust Network Access User Flow Overview Ppt File Deck
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. The Zero Trust Network Access User Flow Overview Ppt File Deck is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.

Cyber Safety Awareness Course Program List Ppt Infographics Shapes PDF
This slide covers list of programs available for increasing security awareness. It includes elements such as programs included for three levels covering essential, advanced and enterprise related services. Showcasing this set of slides titled Cyber Safety Awareness Course Program List Ppt Infographics Shapes PDF. The topics addressed in these templates are Programs, Essentials, Advanced. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Zero Trust Network Access User Flow Overview Software Defined Perimeter SDP
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Retrieve professionally designed Zero Trust Network Access User Flow Overview Software Defined Perimeter SDP to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
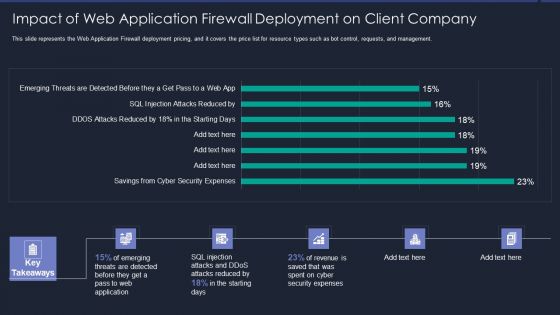
Web App Firewall Services IT Impact Of Web Application Firewall Sample PDF
This slide represents the Web Application Firewall deployment pricing, and it covers the price list for resource types such as bot control, requests, and management. Deliver an awe inspiring pitch with this creative web app firewall services it impact of web application firewall sample pdf bundle. Topics like reduced, security expenses, revenue can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Cyber Exploitation IT Dashboard For Threat Tracking Topics PDF
This slide depicts the dashboard for threat tracking through cyber security measures and ethical hackers by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Deliver an awe inspiring pitch with this creative cyber exploitation it dashboard for threat tracking topics pdf bundle. Topics like dashboard for threat tracking can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Exploitation IT Purpose Of Ethical Hacking Portrait PDF
This slide depicts the purpose of ethical hacking, including the tools and tactics they use and their responsibility to report the discovered vulnerabilities to the authorities. Deliver an awe inspiring pitch with this creative cyber exploitation it purpose of ethical hacking portrait pdf bundle. Topics like vulnerabilities, management, process, weaknesses, security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
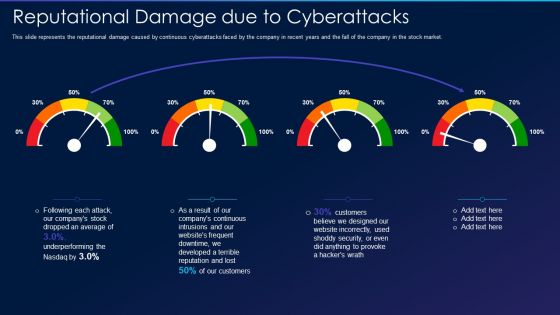
Cyber Exploitation IT Reputational Damage Due To Cyberattacks Professional PDF
This slide represents the reputational damage caused by continuous cyberattacks faced by the company in recent years and the fall of the company in the stock market. Deliver an awe inspiring pitch with this creative cyber exploitation it reputational damage due to cyberattacks professional pdf bundle. Topics like continuous, developed, security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
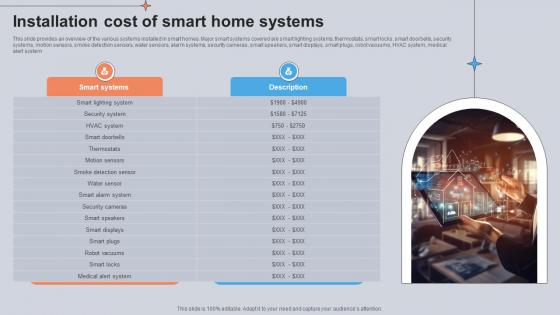
Installation Cost Of Smart Home Systems Utilizing Smart Appliances IoT SS V
This slide provides an overview of the various systems installed in smart homes. Major smart systems covered are smart lighting systems, thermostats, smart locks, smart doorbells, security systems, motion sensors, smoke detection sensors, water sensors, alarm systems, security cameras, smart speakers, smart displays, smart plugs, robot vacuums, HVAC system, medical alert system. Are you searching for a Installation Cost Of Smart Home Systems Utilizing Smart Appliances IoT SS V that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Installation Cost Of Smart Home Systems Utilizing Smart Appliances IoT SS V from Slidegeeks today.

Table Of Contents For Web Development Clipart PDF
This is a Table Of Contents For Web Development Clipart PDF template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Development Technique, Embedded Web Development, Security Web Development You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Threat Management At Workplace Threat Management Action Plan Responsible Person Template PDF
The threat management action plan will help in keeping the track of potential threats that are existing and what are their level, what are the resources required to handle them. The person responsible in handling the threat will keep track of the threat resolve duration and will check whether the threat is treated or not. Deliver and pitch your topic in the best possible manner with this threat management at workplace threat management action plan responsible person template pdf. Use them to share invaluable insights on cyber incident recovery coordination through meetings, confidential information security at risk, cyber security officer and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

 Home
Home