Access Icon
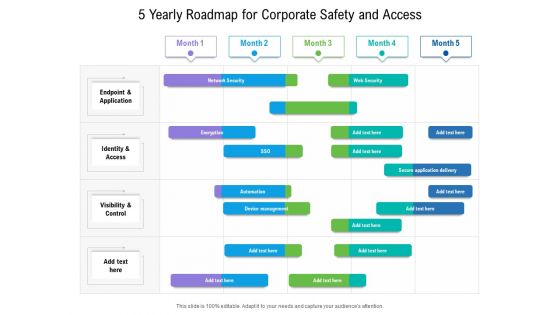
5 Yearly Roadmap For Corporate Safety And Access Sample
We present our 5 yearly roadmap for corporate safety and access sample. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched 5 yearly roadmap for corporate safety and access sample in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
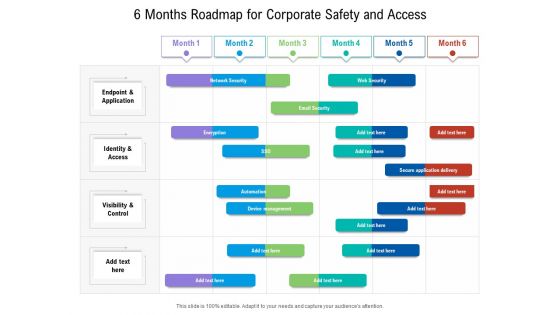
6 Months Roadmap For Corporate Safety And Access Demonstration
We present our 6 months roadmap for corporate safety and access demonstration. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched 6 months roadmap for corporate safety and access demonstration in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
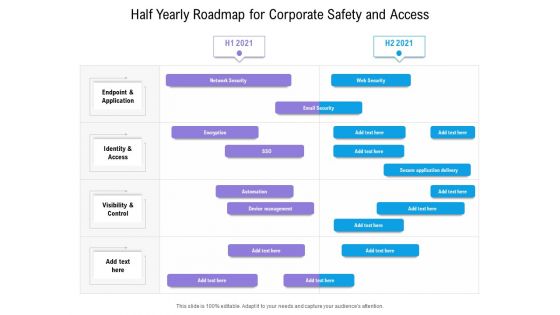
Half Yearly Roadmap For Corporate Safety And Access Ideas
We present our half yearly roadmap for corporate safety and access ideas. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched half yearly roadmap for corporate safety and access ideas in different formats like PDF, PNG, and JPG to smoothly execute your business plan.

Quarterly Roadmap For Corporate Safety And Access Graphics
We present our quarterly roadmap for corporate safety and access graphics. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched quarterly roadmap for corporate safety and access graphics in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
Benefits Access Management Ppt PowerPoint Presentation Professional Smartart Cpb
Presenting this set of slides with name benefits access management ppt powerpoint presentation professional smartart cpb. This is an editable Powerpoint four stages graphic that deals with topics like benefits access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Matrix For Public And Private Blockchains Structure PDF
This slide represents the access matrix for the public and private blockchain types. The purpose of this slide is to showcase the blockchain access, blockchain scope, service and application matrix for public and private blockchain technologies. Find a pre-designed and impeccable Access Matrix For Public And Private Blockchains Structure PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Access Regulations Technology Five Years Roadmap For Biometrics Solution Portrait
We present our access regulations technology five years roadmap for biometrics solution portrait. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched access regulations technology five years roadmap for biometrics solution portrait in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
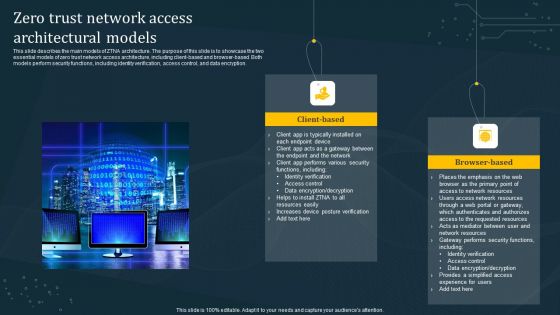
Zero Trust Network Access Architectural Models Diagrams PDF
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. Are you searching for a Zero Trust Network Access Architectural Models Diagrams PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Zero Trust Network Access Architectural Models Diagrams PDF from Slidegeeks today.

Application Of AI For Database Access Governance Summary PDF
This slide represents the applications of artificial intelligence systems for data access governance. The purpose of this slide is to demonstrate the AI application in secure data access. The use cases include threat detection and prediction, system configuration, adaptability, data interpretation, and predictive forecasting. Presenting Application Of AI For Database Access Governance Summary PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prediction, System Configuration, Adaptability. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Ethical Hacking Phase 4 Maintaining Access Ppt Professional Grid PDF
This slide represents the maintaining access phase of ethical hacking and how ethical hackers take advantage of it to detect any malicious activities and prevent them. This is a ethical hacking phase 4 maintaining access ppt professional grid pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like system, information, determining. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
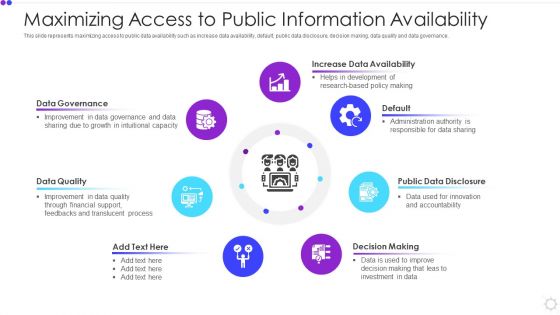
Maximizing Access To Public Information Availability Rules PDF
This slide represents maximizing access to public data availability such as increase data availability, default, public data disclosure, decision making, data quality and data governance. Presenting maximizing access to public information availability rules pdf to dispense important information. This template comprises seven stages. It also presents valuable insights into the topics including data governance, data quality, decision making. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Role Based Access Control RBAC Flow Chart Slides PDF
This slide represents the flow chart of role based access control in an enterprise. It starts with security check on accumulated modifications, application and authentication services and ends with operation on isolated object. Persuade your audience using this Role Based Access Control RBAC Flow Chart Slides PDF. This PPT design covers One stage, thus making it a great tool to use. It also caters to a variety of topics including Operation On Object, Operation On Isolated Object. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
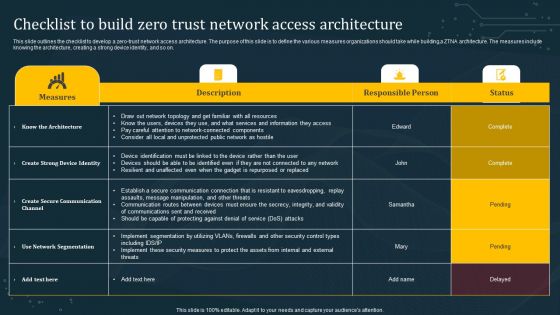
Checklist To Build Zero Trust Network Access Architecture Diagrams PDF
This slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Checklist To Build Zero Trust Network Access Architecture Diagrams PDF can be your best option for delivering a presentation. Represent everything in detail using Checklist To Build Zero Trust Network Access Architecture Diagrams PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
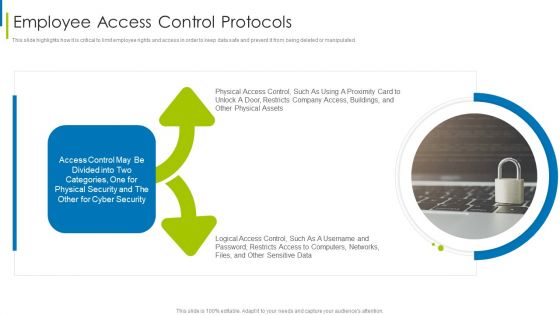
Cyber Terrorism Assault Employee Access Control Protocols Diagrams PDF
This slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated.This is a cyber terrorism assault employee access control protocols diagrams pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Distributed Denial Of Service DDOS As Cyber Terrorism Tool You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Key Pillars Of Identify And Access Management Technique Topics PDF
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Presenting Key Pillars Of Identify And Access Management Technique Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Provisioning Identities, Security Certification, Security Management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Top Tenets Of Zero Trust Network Access Model Brochure PDF
Make sure to capture your audiences attention in your business displays with our gratis customizable Top Tenets Of Zero Trust Network Access Model Brochure PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Access Regulations Technology Half Yearly Roadmap For Biometrics Solution Diagrams
Introducing our access regulations technology half yearly roadmap for biometrics solution diagrams. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.

Access Regulations Technology Five Years Roadmap With Security Solution Inspiration
Presenting our innovatively structured access regulations technology five years roadmap with security solution inspiration Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.

Access Regulations Technology Six Months Roadmap With Security Solution Brochure
Introducing our access regulations technology six months roadmap with security solution brochure. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.
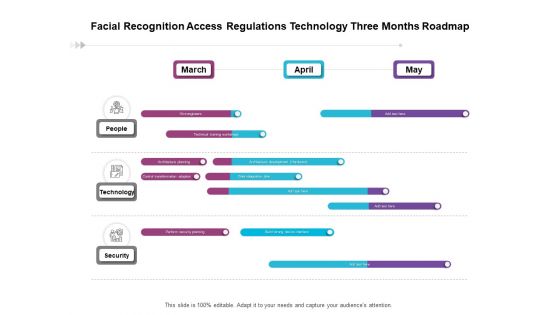
Facial Recognition Access Regulations Technology Three Months Roadmap Formats
Presenting our jaw dropping facial recognition access regulations technology three months roadmap formats. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually appealing design by clicking the download button given below.
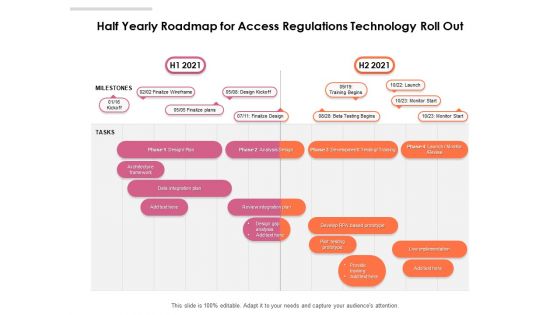
Half Yearly Roadmap For Access Regulations Technology Roll Out Topics
Introducing our half yearly roadmap for access regulations technology roll out topics. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.

Quarterly Roadmap For Access Regulations Technology Roll Out Demonstration
Presenting our jaw dropping quarterly roadmap for access regulations technology roll out demonstration. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually appealing design by clicking the download button given below.
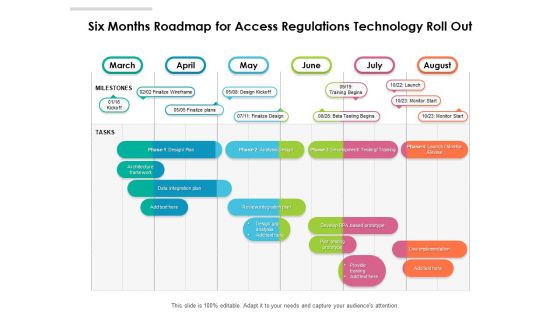
Six Months Roadmap For Access Regulations Technology Roll Out Summary
Presenting our innovatively structured six months roadmap for access regulations technology roll out summary Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.
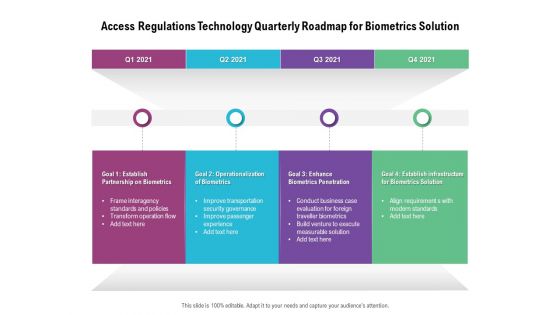
Access Regulations Technology Quarterly Roadmap For Biometrics Solution Background
Presenting our jaw dropping access regulations technology quarterly roadmap for biometrics solution background. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually appealing design by clicking the download button given below.

Access Regulations Technology Six Months Roadmap For Biometrics Solution Mockup
Presenting our innovatively structured access regulations technology six months roadmap for biometrics solution mockup Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.

FDDI Deployment Mac Medium Access Control Layer Designs PDF
This slide explains the medium layer as the responsible layer for identifying addresses as well as creating and verifying FCS and also specifies how to handle the synchronous and asynchronous data flow. Whether you have daily or monthly meetings, a brilliant presentation is necessary. FDDI Deployment Mac Medium Access Control Layer Designs PDF can be your best option for delivering a presentation. Represent everything in detail using FDDI Deployment Mac Medium Access Control Layer Designs PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
Internet Computer World Access PowerPoint Slides And Ppt Diagram Templates
Internet computer world access PowerPoint Slides And PPT Diagram TemplatesThese high quality, editable pre-designed powerpoint slides have been carefully created by our professional team to help you impress your audience. Each graphic in every slide is vector based and is 100% editable in powerpoint. Each and every property of any slide - color, size, shading etc can be modified to build an effective powerpoint presentation. Use these slides to convey complex business concepts in a simplified manner. Any text can be entered at any point in the powerpoint slide. Simply DOWNLOAD, TYPE and PRESENT!
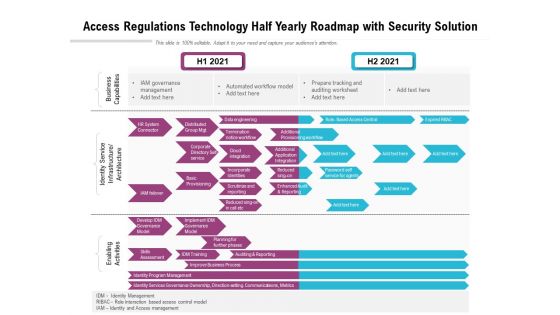
Access Regulations Technology Half Yearly Roadmap With Security Solution Guidelines
Presenting the access regulations technology half yearly roadmap with security solution guidelines. The template includes a roadmap that can be used to initiate a strategic plan. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your needs. This PPT slide can be easily reached in standard screen and widescreen aspect ratios. The set is also available in various formats like PDF, PNG, and JPG. So download and use it multiple times as per your knowledge.
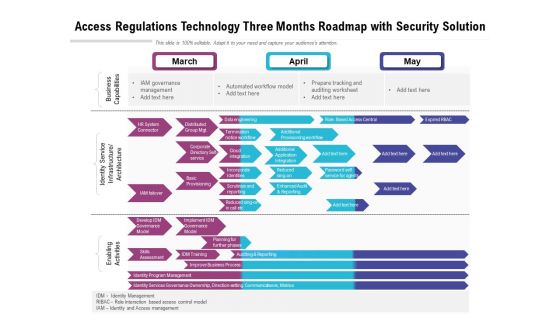
Access Regulations Technology Three Months Roadmap With Security Solution Guidelines
Presenting our jaw dropping access regulations technology three months roadmap with security solution guidelines. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually appealing design by clicking the download button given below.

Facial Recognition Access Regulations Technology Six Months Roadmap Background
Presenting the facial recognition access regulations technology six months roadmap background. The template includes a roadmap that can be used to initiate a strategic plan. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your needs. This PPT slide can be easily reached in standard screen and widescreen aspect ratios. The set is also available in various formats like PDF, PNG, and JPG. So download and use it multiple times as per your knowledge.
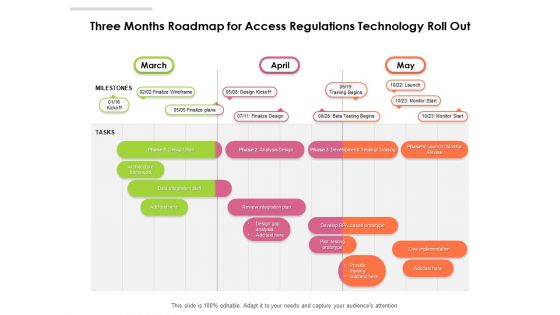
Three Months Roadmap For Access Regulations Technology Roll Out Slides
Presenting the three months roadmap for access regulations technology roll out slides. The template includes a roadmap that can be used to initiate a strategic plan. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your needs. This PPT slide can be easily reached in standard screen and widescreen aspect ratios. The set is also available in various formats like PDF, PNG, and JPG. So download and use it multiple times as per your knowledge.
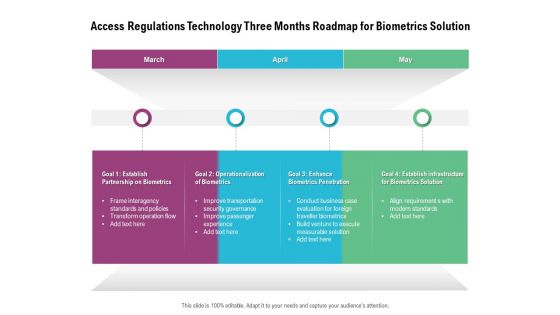
Access Regulations Technology Three Months Roadmap For Biometrics Solution Ideas
Presenting the access regulations technology three months roadmap for biometrics solution ideas. The template includes a roadmap that can be used to initiate a strategic plan. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your needs. This PPT slide can be easily reached in standard screen and widescreen aspect ratios. The set is also available in various formats like PDF, PNG, and JPG. So download and use it multiple times as per your knowledge.
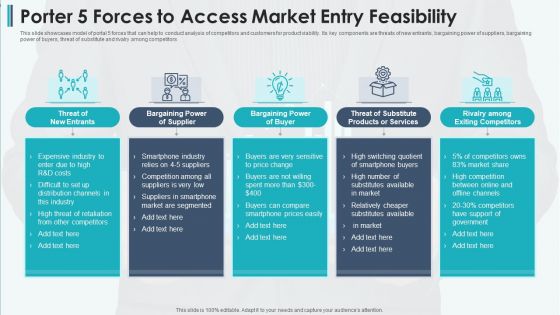
Porter 5 Forces To Access Market Entry Feasibility Professional PDF
This slide showcases model of portal 5 forces that can help to conduct analysis of competitors and customers for product viability. Its key components are threats of new entrants, bargaining power of suppliers, bargaining power of buyers, threat of substitute and rivalry among competitors Presenting porter 5 forces to access market entry feasibility professional pdf to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including bargaining power of supplier, bargaining power of buyer, threat of substitute products or services This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Cloud-Based Identify And Access Management Technique Best Practices Slides PDF
This slide shows ideal practices for IAM strategy. The purpose of this strategy is to highlight all effective practices along with concerned activities. It include practices such as defining IAM vision, building strong foundation , etc. Presenting Cloud-Based Identify And Access Management Technique Best Practices Slides PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Vision Clearly, Strong Foundation, Secure Generic Accounts. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Identity Card Employee Access Ppt PowerPoint Presentation Complete Deck
This identity card employee access ppt powerpoint presentation complete deck acts as backup support for your ideas, vision, thoughts, etc. Use it to present a thorough understanding of the topic. This PPT slideshow can be utilized for both in-house and outside presentations depending upon your needs and business demands. Entailing twelve slides with a consistent design and theme, this template will make a solid use case. As it is intuitively designed, it suits every business vertical and industry. All you have to do is make a few tweaks in the content or any other component to design unique presentations. The biggest advantage of this complete deck is that it can be personalized multiple times once downloaded. The color, design, shapes, and other elements are free to modify to add personal touches. You can also insert your logo design in this PPT layout. Therefore a well-thought and crafted presentation can be delivered with ease and precision by downloading this identity card employee access ppt powerpoint presentation complete deck PPT slideshow.
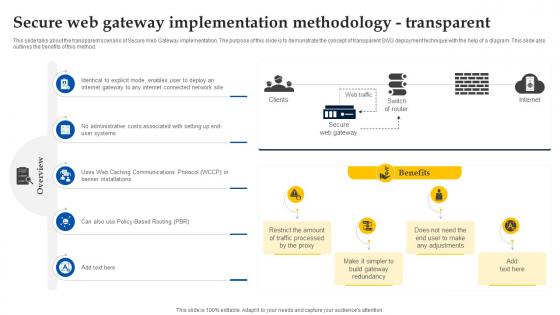
Secure Web Gateway Implementation Methodology Transparent Web Access Control Solution
This slide talks about the transparent scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of transparent SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Secure Web Gateway Implementation Methodology Transparent Web Access Control Solution for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Access Card Employee Corporate Ppt PowerPoint Presentation Complete Deck
If designing a presentation takes a lot of your time and resources and you are looking for a better alternative, then this access card employee corporate ppt powerpoint presentation complete deck is the right fit for you. This is a prefabricated set that can help you deliver a great presentation on the topic. All the twelve slides slides included in this sample template can be used to present a birds-eye view of the topic. These slides are also fully editable, giving you enough freedom to add specific details to make this layout more suited to your business setting. Apart from the content, all other elements like color, design, theme are also replaceable and editable. This helps in designing a variety of presentations with a single layout. Not only this, you can use this PPT design in formats like PDF, PNG, and JPG once downloaded. Therefore, without any further ado, download and utilize this sample presentation as per your liking.
Stock Photo Google Maps Location Access PowerPoint Slide
Use this google maps image slide to make presentations related to technology, satellites, GPS or wireless networks. Design your presentation with this amazing slide and impress your audiences.
Business Diagram Lock Graphics For Secure Internet Access Presentation Template
This power point template has been crafted with graphic of 3d world map and lock. This PPT contains the concept of security. Use this PPT for your business and marketing related presentations.

Access All Areas Internet PowerPoint Themes And PowerPoint Slides 0511
Microsoft PowerPoint Theme and Slide with concept of the internet depicting wide variety of resources available
Secure Internet Access Computer PowerPoint Themes And PowerPoint Slides 0811
Microsoft PowerPoint Theme and Slide with transparent internet browser with a large chrome key protruding out from the window

Effective Data Arrangement For Data Accessibility And Processing Readiness Data Preparation Process Step 2 Discover And Access Data Diagrams PDF
This slide shows the second step that is involved in the data preparation process i.e. discover and access data along with the details. This is a effective data arrangement for data accessibility and processing readiness data preparation process step 2 discover and access data diagrams pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like data preparation process step 2 discover and access data. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
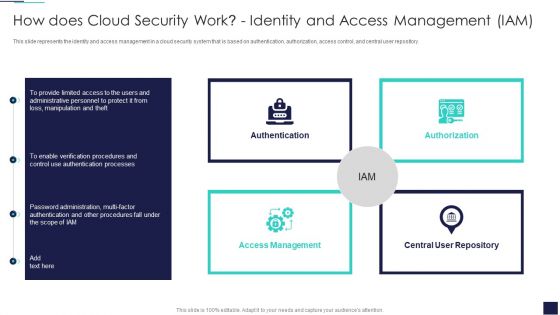
Cloud Information Security How Does Cloud Security Work Identity And Access Management IAM Formats PDF
This slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Presenting Cloud Information Security How Does Cloud Security Work Identity And Access Management IAM Formats PDF to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Central Repository, Access Management, Authorization Authentication. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
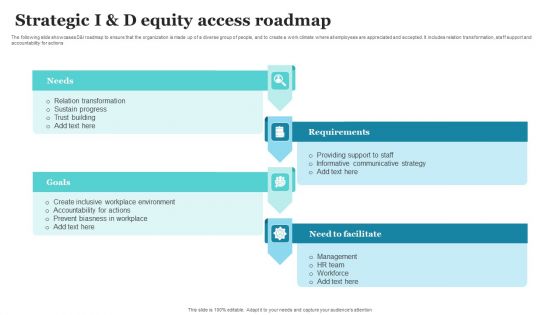
Strategic I And D Equity Access Roadmap Ppt PowerPoint Presentation Gallery Ideas PDF
The following slide showcases DandI roadmap to ensure that the organization is made up of a diverse group of people, and to create a work climate where all employees are appreciated and accepted. It includes relation transformation, staff support and accountability for actions. Presenting Strategic I And D Equity Access Roadmap Ppt PowerPoint Presentation Gallery Ideas PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Needs, Requirements, Need To Facilitate, Goals. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
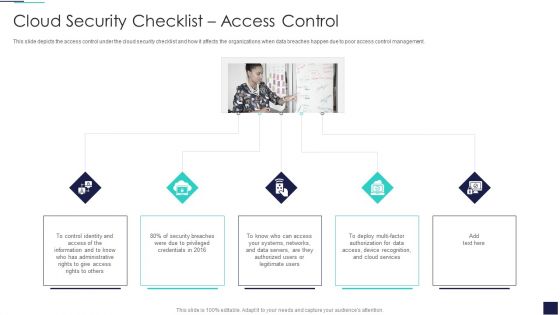
Cloud Information Security Cloud Security Checklist Access Control Ppt Inspiration Professional PDF
This slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. This is a Cloud Information Security Cloud Security Checklist Access Control Ppt Inspiration Professional PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Control Identity, Security Breaches, Data Servers. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

ERP Software Solutions With Access Control Ppt PowerPoint Presentation Portfolio Pictures PDF
Presenting erp software solutions with access control ppt powerpoint presentation portfolio pictures pdf to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including access control, human resources, finance accounting, engineering, project management, data services, crm, purchasing. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
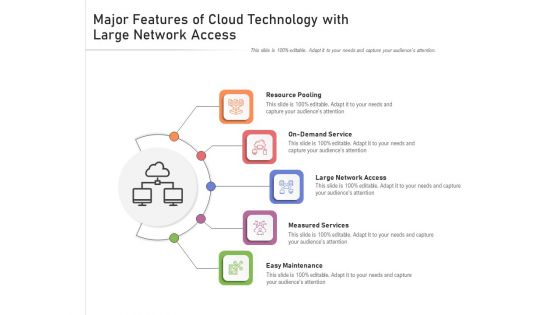
Major Features Of Cloud Technology With Large Network Access Ppt PowerPoint Presentation Gallery Graphics Pictures PDF
Presenting major features of cloud technology with large network access ppt powerpoint presentation gallery graphics pictures pdf to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including resource pooling, on demand service, large network access, measured services, easy maintenance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Integrating Data Privacy System Monitor Access To Sensitive And Regulated Data Sample PDF
This slide explains we help you with data privacy by monitoring access of sensitive and regulated data, in which automation engine assists you in achieving the least privilege and compliance faster. Find a pre-designed and impeccable Integrating Data Privacy System Monitor Access To Sensitive And Regulated Data Sample PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

1 Wireless Computer Networking Wifi Access Point Connected To Globe Computers Ppt Slides
This image slide displays wireless computer networking Wi-Fi access point connected to globe computers. This image slide has been designed with graphic of globe, wireless router and various technology devices. This image slide depicts networking. You may change size, color and orientation of any icon to your liking. Use this PowerPoint template to express views on global, wireless networking in your presentations. This image may also be used in computer education presentations. This image slide will impart professional appearance to your presentations.

1 Wifi Access Point Connected To Mobile Phone And Laptop Over Wireless Network Ppt Slides
This image slide displays Wi-Fi access point connected various technology devices. This image slide has been designed with graphic of wireless router, mobile phone, laptop and computer. This image slide depicts networking. You may change size, color and orientation of any icon to your liking. Use this PowerPoint template to express views on wireless networking in your presentations. This image may also be used in computer education presentations. This image slide will impart professional appearance to your presentations.

1 Wireles Access Point Communication With Mobile Laptop Desktop Computers Ppt Slide
This image slide displays wireless network. This image slide has been designed with graphic of laptops, desktops, mobile, router and WI-FI signal. You may change color, size and orientation of any icon to your liking. Use this image slide, in your presentations to express views on wireless networking, communication and technology. This image slide will enhance the quality of your presentations.
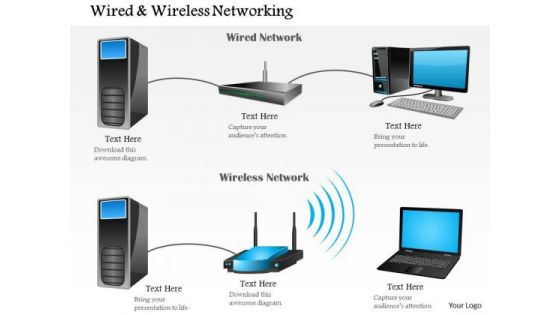
1 Wired And Wireless Networking Shown With Router And Access Point Ppt Slide
This image slide explain the concept of wired and wireless communication. This image slide has been designed with graphic of one wired network with desktop, server and router and one wireless network with server, router and laptop. You may change color, size and orientation of any icon to your liking. Use this image slide, in your presentations to express views on different types of network, communication and technology. This image slide will help you create interesting presentations.

Models Of Access To Information Digital Signage In Internal Communication Channels Slides Pdf
This slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Want to ace your presentation in front of a live audience Our Models Of Access To Information Digital Signage In Internal Communication Channels Slides Pdf can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
Power BI Restrict Access Report In Powerpoint And Google Slides Cpb
Presenting our innovatively-designed set of slides titled Power BI Restrict Access Report In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Power BI Restrict Access Report that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well-structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.

Zero Trust Network Access Vs Virtual Private Network Ppt File Example File
This slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Are you searching for a Zero Trust Network Access Vs Virtual Private Network Ppt File Example File that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Zero Trust Network Access Vs Virtual Private Network Ppt File Example File from Slidegeeks today.

Zero Trust Network Access System Use Cases Software Defined Perimeter SDP
This slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Are you searching for a Zero Trust Network Access System Use Cases Software Defined Perimeter SDP that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Zero Trust Network Access System Use Cases Software Defined Perimeter SDP from Slidegeeks today.
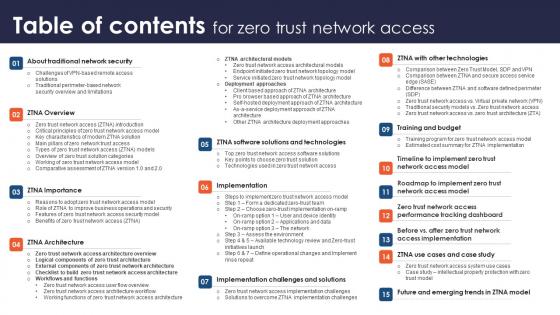
Table Of Contents For Zero Trust Network Access Ppt Diagram Lists
Whether you have daily or monthly meetings, a brilliant presentation is necessary. Table Of Contents For Zero Trust Network Access Ppt Diagram Lists can be your best option for delivering a presentation. Represent everything in detail using Table Of Contents For Zero Trust Network Access Ppt Diagram Lists and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Web Access Control Solution Understanding Real World Use Cases Of Secure Web Gateway
This slide outlines the prominent features of Secure Web Gateway which provide protection to organizations from severe cyber threats. The purpose of this slide is to define the use cases of SWG such as real time web traffic surveillance, access management, etc. If you are looking for a format to display your unique thoughts, then the professionally designed Web Access Control Solution Understanding Real World Use Cases Of Secure Web Gateway is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Web Access Control Solution Understanding Real World Use Cases Of Secure Web Gateway and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
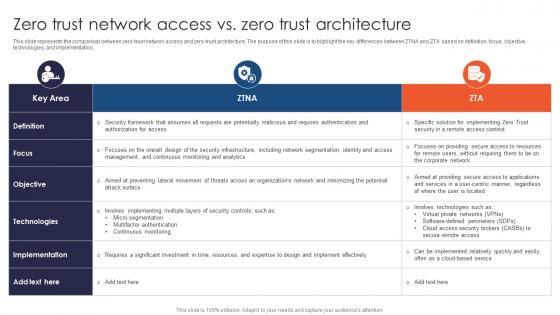
Zero Trust Network Access Vs Zero Trust Architecture Ppt File Infographic Template
This slide represents the comparison between zero-trust network access and zero-trust architecture. The purpose of this slide is to highlight the key differences between ZTNA and ZTA based on definition, focus, objective, technologies, and implementation. Retrieve professionally designed Zero Trust Network Access Vs Zero Trust Architecture Ppt File Infographic Template to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
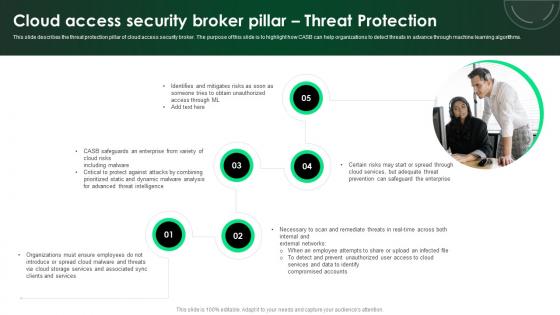
CASB 2 0 IT Cloud Access Security Broker Pillar Threat Protection
This slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Retrieve professionally designed CASB 2 0 IT Cloud Access Security Broker Pillar Threat Protection to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.

 Home
Home