It and cybersecurity PowerPoint Presentation Templates and Google Slides
-
Quantum Computing For Everyone IT Cybersecurity And Cryptography With Quantum Computing Ideas PDF
This slide shows quantum computing in cybersecurity and cryptography and how data will be encrypted through quantum algorithms. Presenting quantum computing for everyone it cybersecurity and cryptography with quantum computing ideas pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like cryptography, quantum computing, cyberattacks, globally. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
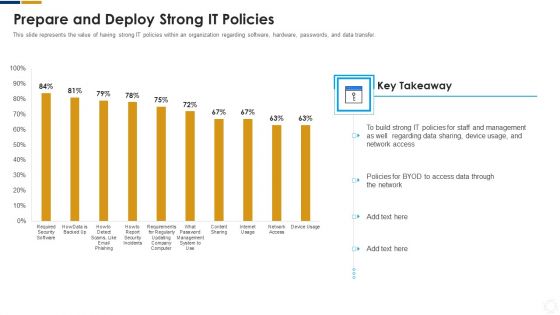
Cybersecurity Prepare And Deploy Strong IT Policies Ppt Pictures Slides PDF
This slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver and pitch your topic in the best possible manner with this cybersecurity prepare and deploy strong it policies ppt pictures slides pdf. Use them to share invaluable insights on management, device, network and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-
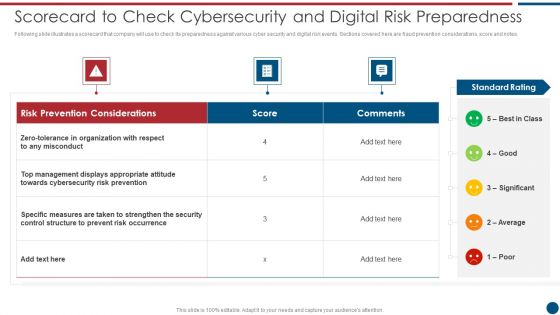
Risk Based Procedures To IT Security Scorecard To Check Cybersecurity And Digital Risk Preparedness Professional PDF
Following slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes. Deliver and pitch your topic in the best possible manner with this Risk Based Procedures To IT Security Scorecard To Check Cybersecurity And Digital Risk Preparedness Professional PDF. Use them to share invaluable insights on Risk Prevention, Risk Prevention, Risk Occurrence and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-
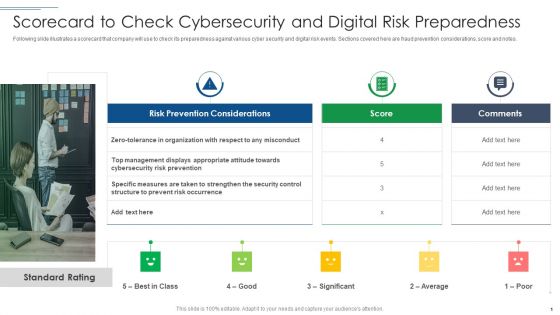
IT Security Risk Management Approach Introduction Scorecard To Check Cybersecurity And Digital Graphics PDF
Following slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes. This is a IT Security Risk Management Approach Introduction Scorecard To Check Cybersecurity And Digital Graphics PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Specific Measures, Security Control, Cybersecurity Risk. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
Blockchain And Distributed Ledger Technology Icon For Cybersecurity Brochure PDF
Showcasing this set of slides titled Blockchain And Distributed Ledger Technology Icon For Cybersecurity Brochure PDF. The topics addressed in these templates are Blockchain And Distributed, Ledger Technology, Icon For Cybersecurity. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
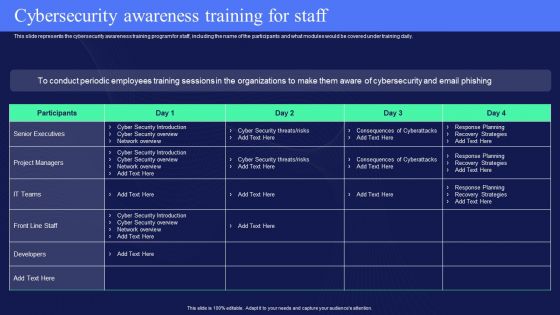
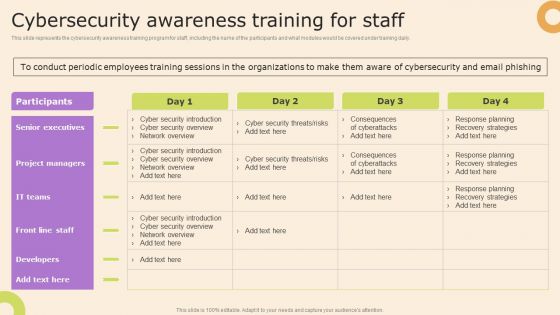
IT Policies And Procedures Cybersecurity Awareness Training For Staff Structure PDF
This slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than IT Policies And Procedures Cybersecurity Awareness Training For Staff Structure PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab IT Policies And Procedures Cybersecurity Awareness Training For Staff Structure PDF today and make your presentation stand out from the rest.
-
Post It Notes Cybersecurity Risk Assessment And Administration Plan Rules PDF
Create an editable Post It Notes Cybersecurity Risk Assessment And Administration Plan Rules PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. ZZZZZZZZZZZZZZZZZZ is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
Information Technology Policy And Processes Cybersecurity Awareness Training For Staff Themes PDF
This slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Information Technology Policy And Processes Cybersecurity Awareness Training For Staff Themes PDF can be your best option for delivering a presentation. Represent everything in detail using Information Technology Policy And Processes Cybersecurity Awareness Training For Staff Themes PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
-
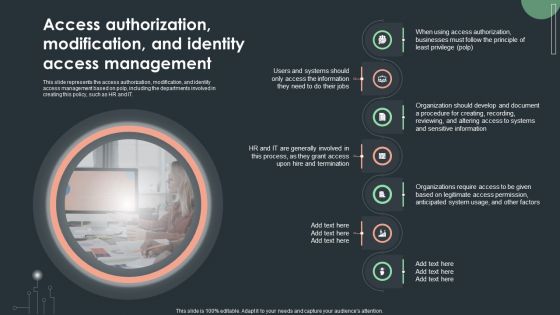
Cybersecurity Guidelines IT Access Authorization Modification And Identity Access Inspiration PDF
This slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Boost your pitch with our creative Cybersecurity Guidelines IT Access Authorization Modification And Identity Access Inspiration PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
Cybersecurity Guidelines IT Data Classification Policy Overview And Approaches Sample PDF
This slide represents the data classification policy overview and approaches. Approaches include highly restricted, restricted, and internal use and types of data each approach will include. If you are looking for a format to display your unique thoughts, then the professionally designed Cybersecurity Guidelines IT Data Classification Policy Overview And Approaches Sample PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Cybersecurity Guidelines IT Data Classification Policy Overview And Approaches Sample PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
-
Cybersecurity Guidelines IT Email And Chat Policy Objective And Guidelines Introduction PDF
This slide represents the email and chat policy, including its objective and general guidelines. It also includes the ways to ensure email security which covers the installation of antivirus and spam filters. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Cybersecurity Guidelines IT Email And Chat Policy Objective And Guidelines Introduction PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
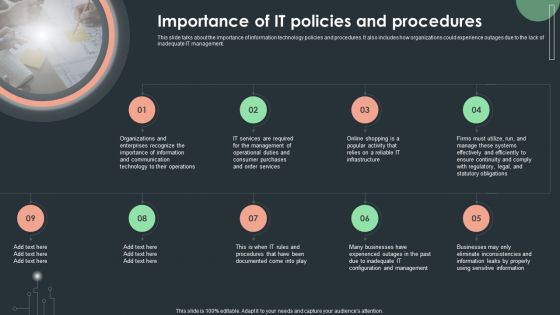
Cybersecurity Guidelines IT Importance Of IT Policies And Procedures Rules PDF
This slide talks about the importance of information technology policies and procedures. It also includes how organizations could experience outages due to the lack of inadequate IT management. Make sure to capture your audiences attention in your business displays with our gratis customizable Cybersecurity Guidelines IT Importance Of IT Policies And Procedures Rules PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
-
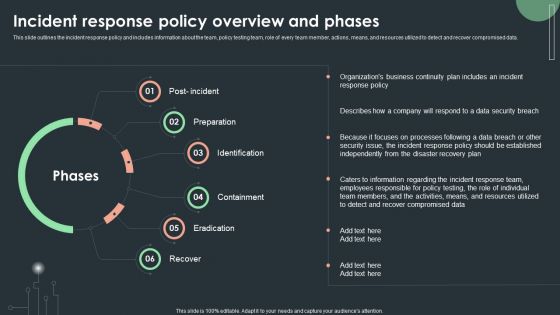
Cybersecurity Guidelines IT Incident Response Policy Overview And Phases Template PDF
This slide outlines the incident response policy and includes information about the team, policy testing team, role of every team member, actions, means, and resources utilized to detect and recover compromised data. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Cybersecurity Guidelines IT Incident Response Policy Overview And Phases Template PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Cybersecurity Guidelines IT Incident Response Policy Overview And Phases Template PDF.
-
Cybersecurity Guidelines IT Internet Usage Policy Objective And General Guidelines Elements PDF
This slide describes the objective and general guidelines of internet usage policy, and it also includes the internet login guidelines for employees. Welcome to our selection of the Cybersecurity Guidelines IT Internet Usage Policy Objective And General Guidelines Elements PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today.
-
Cybersecurity Guidelines IT Password Creation And Management Policy Sample PDF
This slide depicts the password creation and management policy that explains how to create, implement, and review a defined procedure for establishing, updating, and maintaining strong and secure passwords. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Cybersecurity Guidelines IT Password Creation And Management Policy Sample PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
Cybersecurity Guidelines IT Privacy And Company Access To Personal Devices Diagrams PDF
This slide depicts privacy and company access to workers personal devices. It is stated that organizations have the right to analyze personal and work-related data during an emergency. Want to ace your presentation in front of a live audience Our Cybersecurity Guidelines IT Privacy And Company Access To Personal Devices Diagrams PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
Cybersecurity Guidelines IT Security Awareness And Training Policy Overview Portrait PDF
This slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Cybersecurity Guidelines IT Security Awareness And Training Policy Overview Portrait PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Cybersecurity Guidelines IT Security Awareness And Training Policy Overview Portrait PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
-
Cybersecurity Guidelines IT Software Usage Policy Objective And General Guidelines Download PDF
This slide depicts the software usage policy, including its objective, general guidelines, and compliance. This policy covers the instructions regarding both paid and free software. Get a simple yet stunning designed Cybersecurity Guidelines IT Software Usage Policy Objective And General Guidelines Download PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Cybersecurity Guidelines IT Software Usage Policy Objective And General Guidelines Download PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
-
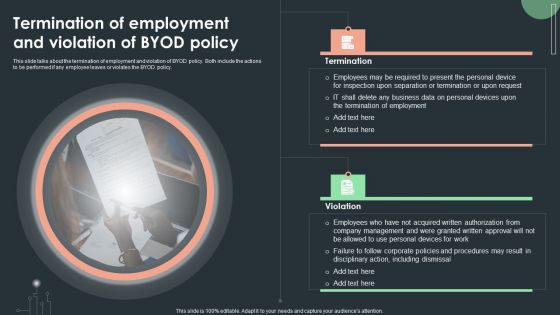
Cybersecurity Guidelines IT Termination Of Employment And Violation Of Byod Policy Themes PDF
This slide talks about the termination of employment and violation of BYOD policy. Both include the actions to be performed if any employee leaves or violates the BYOD policy. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Cybersecurity Guidelines IT Termination Of Employment And Violation Of Byod Policy Themes PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
-
Cybersecurity Guidelines IT Vendor Management Policy Overview And Considerations Diagrams PDF
This slide represents the vendor management policy, and it also includes points to be considered when choosing a vendor. This policy is about the vendor with whom organizations share their critical information. Slidegeeks is here to make your presentations a breeze with Cybersecurity Guidelines IT Vendor Management Policy Overview And Considerations Diagrams PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.