Security

Major Disadvantages Of Using A Hot Wallet Cryptocurrency Management With Blockchain
This slide highlights the disadvantages of using hot wallets in transactions of cryptocurrency. The purpose of this slide is to outline the negatives such as security risks, malware attaches, limited storage, etc.There are so many reasons you need a Major Disadvantages Of Using A Hot Wallet Cryptocurrency Management With Blockchain. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
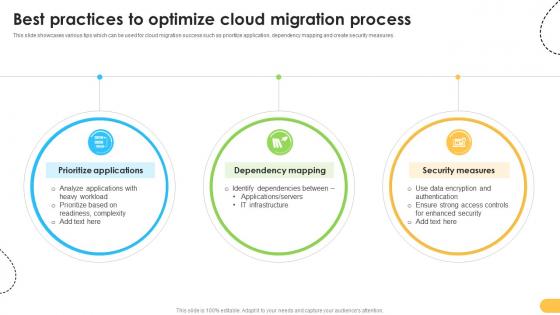
Best Practices To Optimize Cloud Migration Process Data Migration From On Premises
This slide showcases various tips which can be used for cloud migration success such as prioritize application, dependency mapping and create security measures. There are so many reasons you need a Best Practices To Optimize Cloud Migration Process Data Migration From On Premises. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Effective Data Migration Best Practices To Optimize Cloud Migration Process
This slide showcases various tips which can be used for cloud migration success such as prioritize application, dependency mapping and create security measures. There are so many reasons you need a Effective Data Migration Best Practices To Optimize Cloud Migration Process. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Effective Data Migration Suitable Cloud Environment Selection For Migration
This slide showcases selection of profitable cloud environment based on criteria such as ease of set up, data security control and cost effectiveness. There are so many reasons you need a Effective Data Migration Suitable Cloud Environment Selection For Migration. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
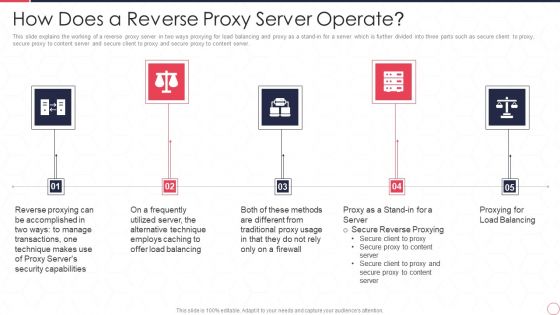
Reverse Proxy Server IT How Does A Reverse Proxy Server Operate Ppt Model Example Introduction PDF
This slide explains the working of a reverse proxy server in two ways proxying for load balancing and proxy as a stand-in for a server which is further divided into three parts such as secure client to proxy, secure proxy to content server and secure client to proxy and secure proxy to content server. Presenting reverse proxy server it how does a reverse proxy server operate ppt model example introduction pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like reverse proxying, technique, servers security capabilities, offer load balancing. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Our Solution Email And Data Protection Platform Capital Funding Pitch Deck PPT Sample
This slide covers key solutions provided by email security application for the problems faced by customers. It includes an email filtering service, secure file sharing, and HIPAA-compliant email encryption. Make sure to capture your audiences attention in your business displays with our gratis customizable Our Solution Email And Data Protection Platform Capital Funding Pitch Deck PPT Sample. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Zero Trust Model Case Study Intellectual Property Protection
This slide represents the case study for implementing the ZTNA security model into a food and beverage organization to secure intellectual property, supply chain and manufacturing. The purpose of this slide is to highlight the key requirements, solutions and impact of ZTNA implementation on the business. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Zero Trust Model Case Study Intellectual Property Protection will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
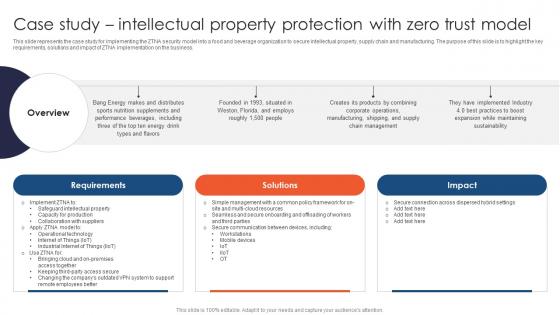
Zero Trust Network Access Case Study Intellectual Property Protection With Zero Trust Model
This slide represents the case study for implementing the ZTNA security model into a food and beverage organization to secure intellectual property, supply chain and manufacturing. The purpose of this slide is to highlight the key requirements, solutions and impact of ZTNA implementation on the business. Make sure to capture your audiences attention in your business displays with our gratis customizable Zero Trust Network Access Case Study Intellectual Property Protection With Zero Trust Model. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
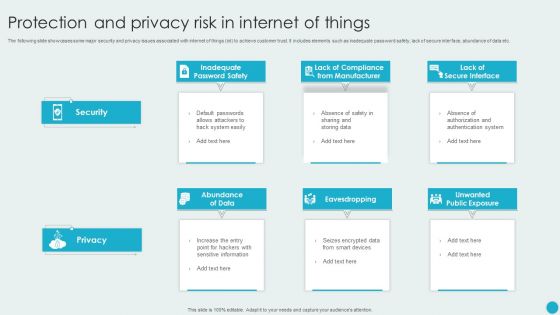
Protection And Privacy Risk In Internet Of Things Topics PDF
The following slide showcases some major security and privacy issues associated with internet of things iot to achieve customer trust. It includes elements such as inadequate password safety, lack of secure interface, abundance of data etc. Presenting Protection And Privacy Risk In Internet Of Things Topics PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Abundance Of Data, Eavesdropping, Unwanted Public Exposure. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Iot Device Authentication Methods To Ensure Data Iot Device Management Download Pdf
This slide showcases several IoT device authentication models for standardise and secure communication between machines. It included modules such as X.509 certificates, hardware security module, trusted platform module, and symmetric keys. Slidegeeks has constructed after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
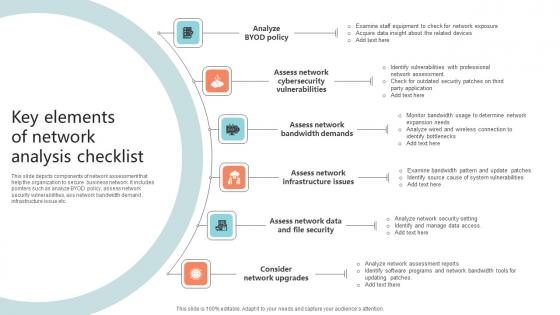
Key Elements Of Network Analysis Checklist Microsoft Pdf
This slide depicts components of network assessment that help the organization to secure business network. It includes pointers such as analyze BYOD policy, assess network security vulnerabilities, ass network bandwidth demand , infrastructure issue etc.Pitch your topic with ease and precision using this Key Elements Of Network Analysis Checklist Microsoft Pdf This layout presents information on Cybersecurity Vulnerabilities, Bandwidth Demands, Assess Network It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

5G Network Technology Value Enabler 1 5G Resilient Networks System Ppt Layouts Diagrams PDF
This slide provides details regarding value enabler for operator as 5G resilient networks system including importance and key components associated to it. This is a 5g network technology value enabler 1 5g resilient networks system ppt layouts diagrams pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like service availability, security assurance, secured identities and protocols. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Value Enabler 1 5G Resilient Networks System 5G Network Architecture Instructions Sample PDF
This slide provides details regarding value enabler for operator as 5G resilient networks system including importance and key components associated to it. Presenting Value Enabler 1 5G Resilient Networks System 5G Network Architecture Instructions Sample PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Service Availability, Security Assurance, Secured Identities. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
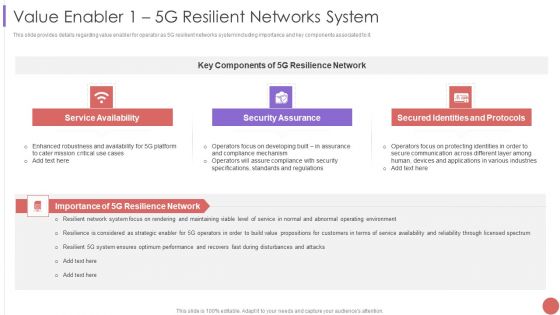
Value Enabler 1 5G Resilient Networks System Professional PDF
This slide provides details regarding value enabler for operator as 5G resilient networks system including importance and key components associated to it. This is a Value Enabler 1 5G Resilient Networks System Professional PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Service Availability, Security Assurance, Secured Identities. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Safety Incident Management Impact Analysis For Effective Threat Management Structure PDF
This slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. This is a cyber safety incident management impact analysis for effective threat management structure pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like impact analysis for effective threat management in securing workplace. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Key Techniques In Phishing Attacks Awareness Training Program Themes PDF
This slide covers strategies to consider in phishing awareness training program. It involves strategies such as verify email address, consider every email as phishing attempt and update security software. Presenting Key Techniques In Phishing Attacks Awareness Training Program Themes PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Implement, Secure Network Connectivity, Payment Service. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
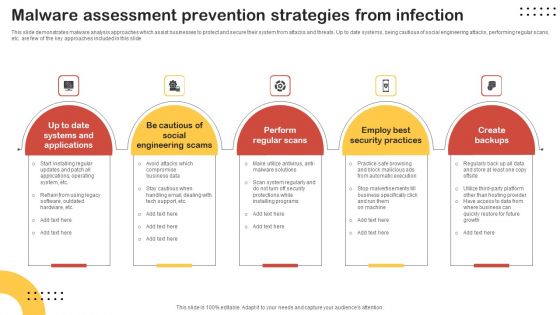
Malware Assessment Prevention Strategies From Infection Topics PDF
This slide demonstrates malware analysis approaches which assist businesses to protect and secure their system from attacks and threats. Up to date systems, being cautious of social engineering attacks, performing regular scans, etc. are few of the key approaches included in this slide. Presenting Malware Assessment Prevention Strategies From Infection Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Perform Regular Scans, Employ Best Security Practices, Create Backups. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
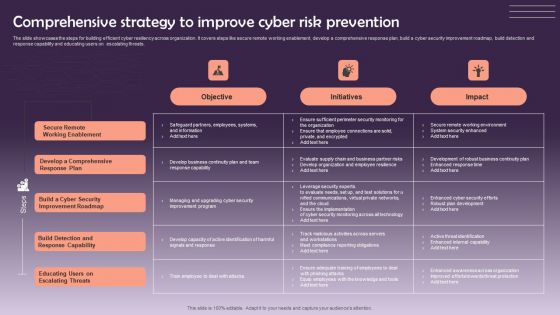
Comprehensive Strategy To Improve Cyber Risk Prevention Graphics PDF
The slide showcases the steps for building efficient cyber resiliency across organization. It covers steps like secure remote working enablement, develop a comprehensive response plan, build a cyber security improvement roadmap, build detection and response capability and educating users on escalating threats. Pitch your topic with ease and precision using this Comprehensive Strategy To Improve Cyber Risk Prevention Graphics PDF. This layout presents information on Objective, Initiatives, Impact. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Cybersecurity Hardware And Software Update In Company Ppt Inspiration Rules PDF
This slide depicts the hardware or software update measure under the cyber security model. It also tells the current status of the devices that need to update in the organization. This is a cybersecurity hardware and software update in company ppt inspiration rules pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like technology, secure, network, systems. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Multi Cloud Complexity Management Managing Compliance In Multi Cloud Environment Pictures PDF
This slide covers the policies for managing compliance in multi cloud such as Securing Cloud User Information, Optimizing Resource Usage And Value, Optimizing System And Resource Usage etc. Deliver and pitch your topic in the best possible manner with this Multi Cloud Complexity Management Managing Compliance In Multi Cloud Environment Pictures PDF. Use them to share invaluable insights on Security Policy, Device And Resource, Network and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Cryptocurrency Ledger Public Blockchain Technology Infographics PDF
This slide depicts the public blockchain technology framework and how data is stored in the public blockchain, bitcoin, voting are few examples of the public blockchain. Presenting Cryptocurrency Ledger Public Blockchain Technology Infographics PDF to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like Network, Secure Method, Security Protocols Sincerely. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
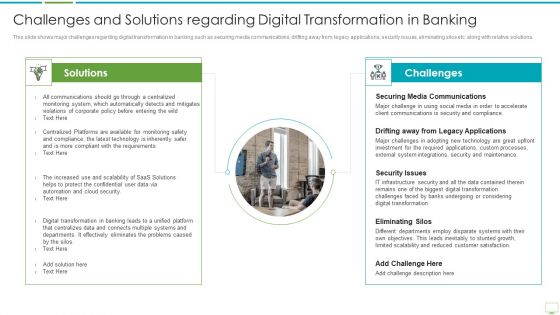
Major Advantages Of Banking Industry Revolution Challenges And Solutions Regarding Diagrams PDF
This slide shows the benefits of mobile banking that improves and enhances the banking services and leads to a positive digital banking transformation such as 24 7 service availability, paperless transactions, facilitation of location-based services, increased efficiency and compliance etc. Presenting major advantages of banking industry revolution challenges and solutions regarding diagrams pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like securing media communications, drifting away from legacy applications, security issues In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
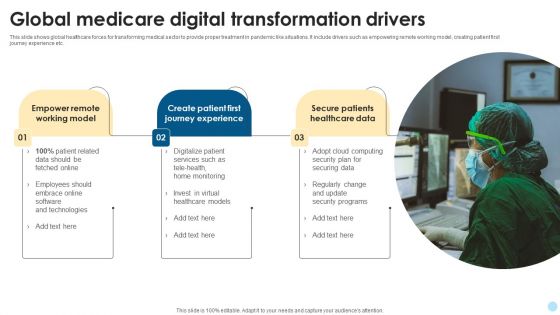
Global Medicare Digital Transformation Drivers Mockup PDF
This slide shows global healthcare forces for transforming medical sector to provide proper treatment in pandemic like situations. It include drivers such as empowering remote working model, creating patient first journey experience etc. Showcasing this set of slides titled Global Medicare Digital Transformation Drivers Mockup PDF. The topics addressed in these templates are Digitalize Patient Services, Security Programs, Securing Data. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Pitch Deck To Raise Capital From Product Pooled Funding Why Should Investors Choose Us Graphics PDF
This slide provides the key values which the company offers to its stakeholders. Key Values include Product quality, Reliability, Affordability, Security etc. Presenting pitch deck to raise capital from product pooled funding why should investors choose us graphics pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like quality, reliable, affordable cost, secure, easy to work with. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
RPA IT Blue Prism Robotic Process Automation Tool Ppt Professional Icon PDF
This slide describes the blue prism tool of the RPA along with the pros, cons and features of the tool such as robust, 24 7 workforce, information security and execution insight. Presenting rpa it blue prism robotic process automation tool ppt professional icon pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like secure and accurate, robust, adaptable and resilient, analytics, execution insight. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Mitigating Cybersecurity Threats And Vulnerabilities Impact Analysis For Effective Threat Graphics PDF
This slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. This is a mitigating cybersecurity threats and vulnerabilities impact analysis for effective threat graphics pdf template with various stages. Focus and dispense information one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like impact analysis for effective threat management in securing workplace. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
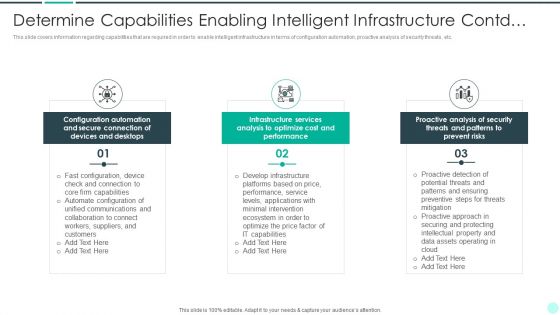
Executing Advance Data Analytics At Workspace Determine Capabilities Enabling Brochure PDF
This slide covers information regarding capabilities that are required in order to enable intelligent infrastructure in terms of configuration automation, proactive analysis of security threats, etc. Presenting executing advance data analytics at workspace determine capabilities enabling brochure pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like secure, connection, devices, optimize. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Big Data Architect Tool Selection For Big Data Management Icons PDF
This slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on.This is a Big Data Architect Tool Selection For Big Data Management Icons PDF template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Businesses Frequently, Straight Forward, Either Providing. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Blue Prism Robotic Process Automation Tool Robotic Process Automation Technology Ideas PDF
This slide describes the blue prism tool of the RPA along with the pros, cons and features of the tool such as robust, 24 or 7 workforce, information security and execution insight.This is a Blue Prism Robotic Process Automation Tool Robotic Process Automation Technology Ideas PDF template with various stages. Focus and dispense information on eight stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Secure Accurate, Adaptable Resilient, Only Programming. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Managing Compliance In Multi Cloud Environment Demonstration PDF
This slide covers the policies for managing compliance in multi cloud such as Securing Cloud User Information, Optimizing Resource Usage and Value, Optimizing System and Resource Usage etc. Presenting Managing Compliance In Multi Cloud Environment Demonstration PDF to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like Security Policy, Capacity Policy, Cost Policy. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Series A Venture Capital Funding Due Diligence Checklist Guidelines PDF
The slide showcases due diligence checklist which helps you to run through all the pieces of information . It covers corporate records and charter documents, business plan and financials, intellectual property, security issuances and agreements concerning securities and material agreements. Presenting Series A Venture Capital Funding Due Diligence Checklist Guidelines PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Business Plan Financials, Material Agreements, Intellectual Property. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Developmental Digital Banking Transformational Drivers Slides PDF
This slide covers trends of digital banking sector. The purpose of these trends is secure data and support banks security norms. These drivers are block chain, upgraded ATM, artificial intelligence and cloud computing. Presenting Developmental Digital Banking Transformational Drivers Slides PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Artificial Intelligence, Block Chain, Cloud Computing. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Enable Cybersecurity Compliance At Organization Mockup PDF
This slide provides details regarding role of cybersecurity compliance at workplace. The importance of the security compliance include management of user trust, enhance business efficiency, secure brand reputation, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Enable Cybersecurity Compliance At Organization Mockup PDF and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
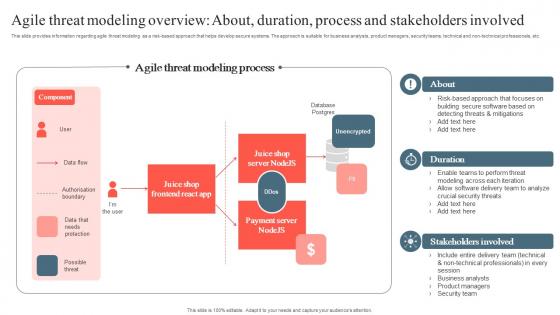
Playbook To Remediate False Agile Threat Modeling Overview About Download Pdf
This slide provides information regarding agile threat modeling as a risk based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non technical professionals, etc. Want to ace your presentation in front of a live audience Our Playbook To Remediate False Agile Threat Modeling Overview About Download Pdf can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.

Exit Strategy Email And Data Protection Platform Capital Funding Pitch Deck PPT Template
This slide covers the exit strategy of the email security software company. It includes various exit options such as merger and acquisition and initial public offering. Present like a pro with Exit Strategy Email And Data Protection Platform Capital Funding Pitch Deck PPT Template. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.

Implement General Data Protection Regulation DT SS V
This slide presents actions to establish a safe-custodian image in retail industry. It includes integrating general data protection and regulation with steps understand GDPR, data audit, consent and legal basis, privacy notices and policies, data security and breach notification and ongoing compliance. Find a pre-designed and impeccable Implement General Data Protection Regulation DT SS V. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Implement General Data Protection Regulation Optimizing Retail Operations With Digital DT SS V
This slide presents actions to establish a safe-custodian image in retail industry. It includes integrating general data protection and regulation with steps understand GDPR, data audit, consent and legal basis, privacy notices and policies, data security and breach notification and ongoing compliance. Find a pre-designed and impeccable Implement General Data Protection Regulation Optimizing Retail Operations With Digital DT SS V. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Ways To Control Cyber Protection And Privacy Issues Diagrams PDF
The following slide illustrates some ways to monitor cybersecurity and privacy issues. It includes activities such as protecting CRM platform, keeping security system updated, modifying passwords regularly etc. Persuade your audience using this Ways To Control Cyber Protection And Privacy Issues Diagrams PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Change Passwords Regularly, Regular Backups, Protect CRM Platform. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
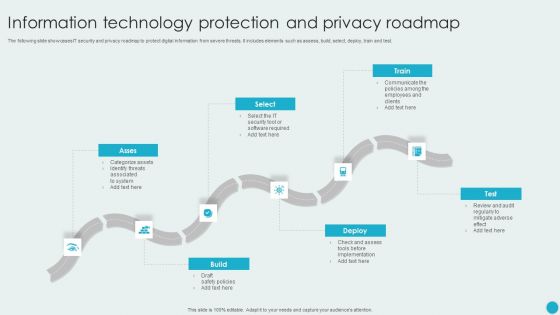
Information Technology Protection And Privacy Roadmap Sample PDF
The following slide showcases IT security and privacy roadmap to protect digital information from severe threats. It includes elements such as assess, build, select, deploy, train and test. Persuade your audience using this Information Technology Protection And Privacy Roadmap Sample PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Deploy, Build, Select, Train. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
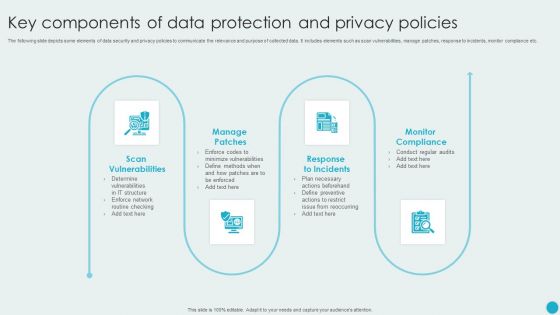
Key Components Of Data Protection And Privacy Policies Graphics PDF
The following slide depicts some elements of data security and privacy policies to communicate the relevance and purpose of collected data. It includes elements such as scan vulnerabilities, manage patches, response to incidents, monitor compliance etc. Presenting Key Components Of Data Protection And Privacy Policies Graphics PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Manage Patches, Response To Incidents, Monitor Compliance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Technologies To Ensure Data Protection And Privacy Background PDF
The following slide showcases some technologies to administer organizational data privacy and security concerns. It includes elements such as data encryption, change management and auditing, user and behavior analytics UEBA, backup and recovery etc. Presenting Technologies To Ensure Data Protection And Privacy Background PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Data Encryption, Change Management And Auditing, Backup And Recovery. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
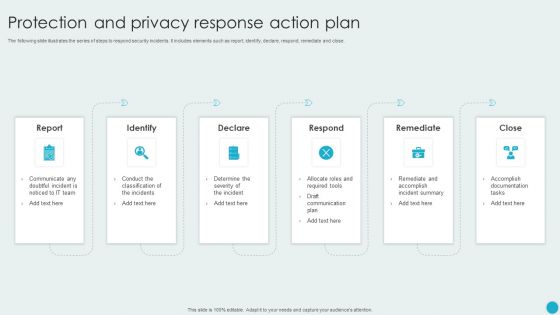
Protection And Privacy Response Action Plan Graphics PDF
The following slide illustrates the series of steps to respond security incidents. It includes elements such as report, identify, declare, respond, remediate and close. Persuade your audience using this Protection And Privacy Response Action Plan Graphics PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Declare, Respond, Remediate, Identify. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Factors Influencing Software Defined Networking Adoption SDN Building Blocks Template Pdf
This slide represents the factors influencing SDN adoption, including cultural change, security risks, interoperability, scalability, performance, and reliability. SDN is appealing regarding network simplicity and investment, and operational cost savings.Slidegeeks has constructed Factors Influencing Software Defined Networking Adoption SDN Building Blocks Template Pdf after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

Two Factor Authentication For Everything About Bitcoin PPT Presentation Fin SS V
This slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Two Factor Authentication For Everything About Bitcoin PPT Presentation Fin SS V and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
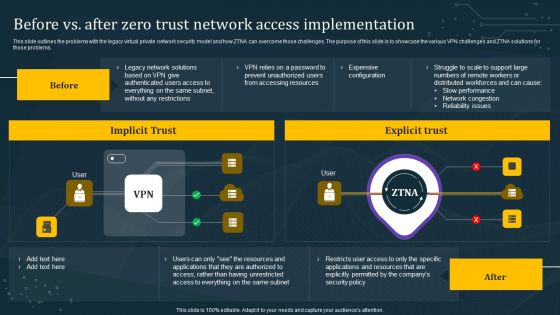
Before Vs After Zero Trust Network Access Implementation Background PDF
This slide outlines the problems with the legacy virtual private network security model and how ZTNA can overcome those challenges. The purpose of this slide is to showcase the various VPN challenges and ZTNA solutions for those problems. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Before Vs After Zero Trust Network Access Implementation Background PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
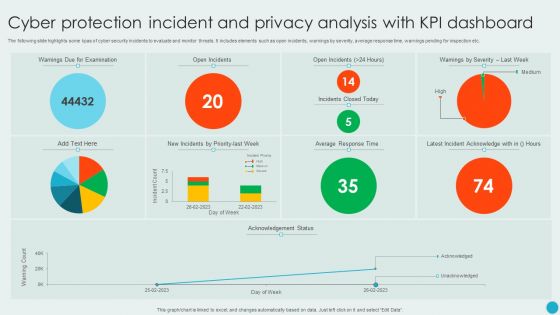
Cyber Protection Incident And Privacy Analysis With KPI Dashboard Ideas PDF
The following slide highlights some kpas of cyber security incidents to evaluate and monitor threats. It includes elements such as open incidents, warnings by severity, average response time, warnings pending for inspection etc. Showcasing this set of slides titled Cyber Protection Incident And Privacy Analysis With KPI Dashboard Ideas PDF. The topics addressed in these templates are Cyber Protection Incident, Privacy Analysis, KPI Dashboard. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
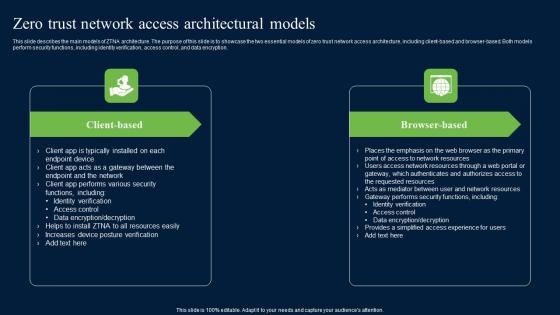
Zero Trust Network Access Architectural Models Ideas Pdf
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. There are so many reasons you need a Zero Trust Network Access Architectural Models Ideas Pdf. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Major Reasons To Manage Online Protection And Privacy Issues Template PDF
The following slide highlights the major causes to administer digital security and privacy concerns. It includes activities such as setting credibility with users, optimizing social media presence, improving marketing efforts etc. Persuade your audience using this Major Reasons To Manage Online Protection And Privacy Issues Template PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Set Credibility With Users, Optimize Social Media Presence, To Reduce Damage Expenses. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
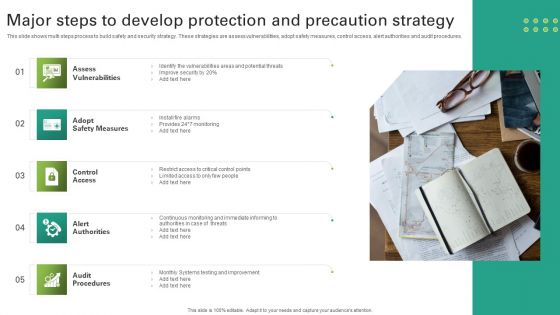
Major Steps To Develop Protection And Precaution Strategy Themes PDF
This slide shows multi steps process to build safety and security strategy. These strategies are assess vulnerabilities, adopt safety measures, control access, alert authorities and audit procedures. Persuade your audience using this Major Steps To Develop Protection And Precaution Strategy Themes PDF. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including Assess Vulnerabilities, Adopt Safety Measures, Control Access. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Large Event Safety And Conveyance Plan Checklist Portrait Pdf
The following slide presents a security and communication plan checklist to be used by managers for checking the status of activities in large event. Key initiatives include budget allocation, number of attendees, seating arrangements etc. Pitch your topic with ease and precision using this Large Event Safety And Conveyance Plan Checklist Portrait Pdf. This layout presents information on Key Initiatives, Safety And Conveyance. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
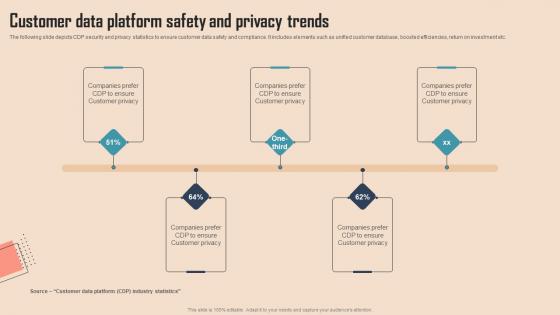
Customer Data Platform Safety And Comprehensive CDP Guide For Promoters Brochure Pdf
The following slide depicts CDP security and privacy statistics to ensure customer data safety and compliance. It includes elements such as unified customer database, boosted efficiencies, return on investment etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Customer Data Platform Safety And Comprehensive CDP Guide For Promoters Brochure Pdf will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Conveyance Technologies In Safety Plan For Large Events Brochure Pdf
This slide presents major communication technologies which can be used by security teams to manage and report incidents in large events. The technologies covered are automated alerts, geofencing capabilities, cloud-based system, etc. Showcasing this set of slides titled Conveyance Technologies In Safety Plan For Large Events Brochure Pdf. The topics addressed in these templates are Automated Alerts, Geofencing Capabilities, Cloud Based System. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
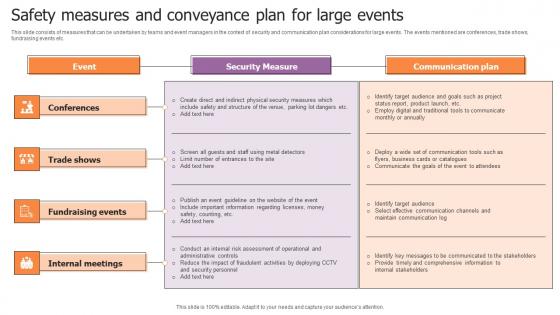
Safety Measures And Conveyance Plan For Large Events Designs Pdf
This slide consists of measures that can be undertaken by teams and event managers in the context of security and communication plan considerations for large events. The events mentioned are conferences, trade shows, fundraising events etc. Pitch your topic with ease and precision using this Safety Measures And Conveyance Plan For Large Events Designs Pdf. This layout presents information on Conferences, Trade Shows, Fundraising Events. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
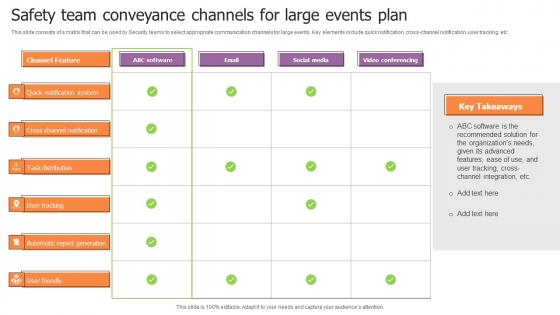
Safety Team Conveyance Channels For Large Events Plan Brochure Pdf
This slide consists of a matrix that can be used by Security teams to select appropriate communication channels for large events. Key elements include quick notification, cross-channel notification, user tracking, etc. Showcasing this set of slides titled Safety Team Conveyance Channels For Large Events Plan Brochure Pdf. The topics addressed in these templates are Channel Feature, Software, Email, Social Media. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Cybersecurity Cyber Safety Tips Protection Against Cyberattacks Ppt Styles Gallery PDF
This slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. This is a cybersecurity cyber safety tips protection against cyberattacks ppt styles gallery pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like systems, network. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
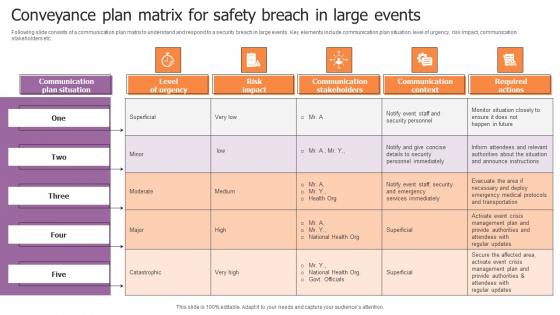
Conveyance Plan Matrix For Safety Breach In Large Events Diagrams Pdf
Following slide consists of a communication plan matrix to understand and respond to a security breach in large events. Key elements include communication plan situation, level of urgency, risk impact, communication stakeholders etc. Pitch your topic with ease and precision using this Conveyance Plan Matrix For Safety Breach In Large Events Diagrams Pdf. This layout presents information on Level Of Urgency, Risk Impact, Communication Stakeholders. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
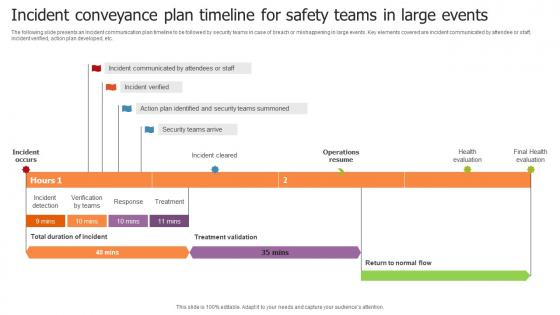
Incident Conveyance Plan Timeline For Safety Teams In Large Events Inspiration Pdf
The following slide presents an Incident communication plan timeline to be followed by security teams in case of breach or mishappening in large events. Key elements covered are incident communicated by attendee or staff, incident verified, action plan developed, etc. Showcasing this set of slides titled Incident Conveyance Plan Timeline For Safety Teams In Large Events Inspiration Pdf. The topics addressed in these templates are Operations Resume, Treatment Validation . All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Overcoming Challenges In Conveyance And Safety Plan For Large Events Clipart Pdf
This slide provides information regarding the usage of a communication plan to address challenges in managing the security of large events. Major challenges covered in the slide relate to planning, access control and rapport management. Pitch your topic with ease and precision using this Overcoming Challenges In Conveyance And Safety Plan For Large Events Clipart Pdf. This layout presents information on Planning Communication, Access Control, Rapport Management. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
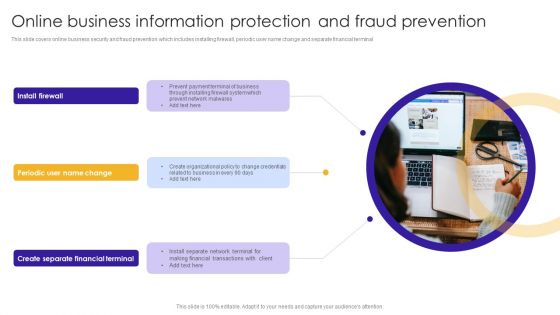
Online Business Information Protection And Fraud Prevention Topics PDF
This slide covers online business security and fraud prevention which includes installing firewall, periodic user name change and separate financial terminal. Persuade your audience using this Online Business Information Protection And Fraud Prevention Topics PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Create Separate, Financial Terminal, Prevent Network. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Strategies For Conveyance Of Large Event Safety Plan Icons Pdf
This slide highlights major strategies to communicate effectively for large event security plans in order to ensure the safety of the business and enhance confidence among stakeholders. Key strategies are to inspect the venue, conduct a risk assessment, assess large-scale attacks, etc. Pitch your topic with ease and precision using this Strategies For Conveyance Of Large Event Safety Plan Icons Pdf. This layout presents information on Inspect The Venue, Conduct Risk Assessment, Crowd Controlling Measures. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

 Home
Home