Hacking
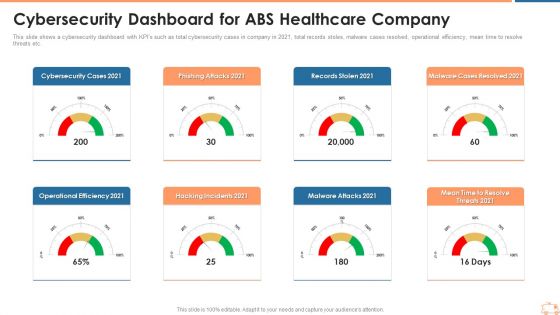
Cybersecurity Dashboard For ABS Healthcare Company Ppt Themes PDF
This slide shows a cybersecurity dashboard with KPIs such as total cybersecurity cases in company in 2021, total records stoles, malware cases resolved, operational efficiency, mean time to resolve threats etc. Presentingcybersecurity dashboard for abs healthcare company ppt themes pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like phishing attacks 2021, records stolen 2021, malware cases resolved 2021, malware attacks 2021, hacking incidents 2021. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Russian Cyber Attacks On Ukraine IT Cyber Attacks On Ukraine Information PDF
This slide represents the conspicuous Russian cyber attacks on Ukraine, including the attacks on government and banking websites, hacking of the countrys railway computer networks, etc. Presenting russian cyber attacks on ukraine it cyber attacks on ukraine information pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like social media, systems, networks, services. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
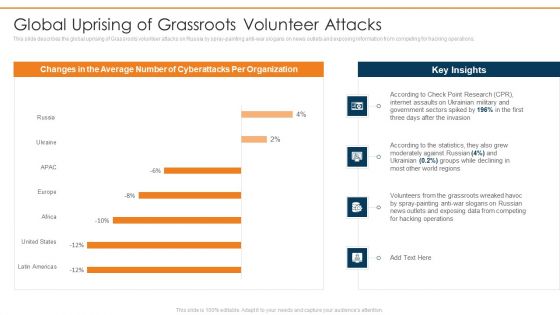
Data Wiper Spyware Attack Global Uprising Of Grassroots Volunteer Attacks Background PDF
This slide describes the global uprising of Grassroots volunteer attacks on Russia by spray-painting anti war slogans on news outlets and exposing information from competing for hacking operations.Deliver an awe inspiring pitch with this creative data wiper spyware attack global uprising of grassroots volunteer attacks background pdf bundle. Topics like according to the statistics, moderately against russian, volunteers from the grassroots can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
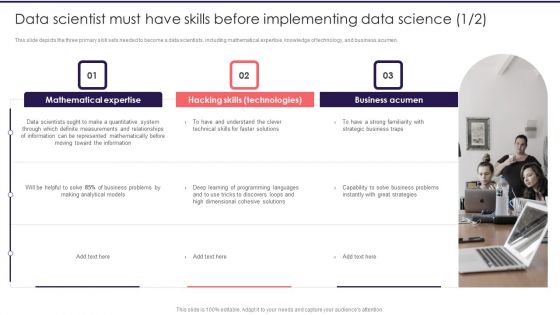
Information Studies Data Scientist Must Have Skills Before Implementing Data Science Slides PDF
This slide depicts the three primary skill sets needed to become a data scientists, including mathematical expertise, knowledge of technology, and business acumen. This is a Information Studies Data Scientist Must Have Skills Before Implementing Data Science Slides PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Mathematical Expertise, Business Acumen, Hacking Skills. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
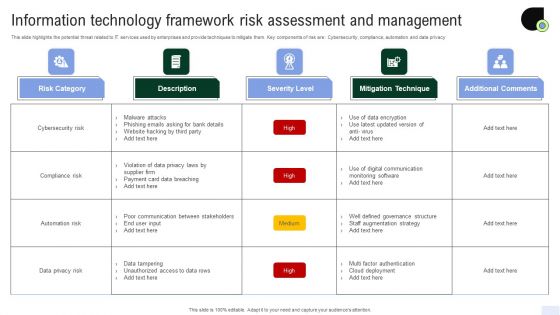
Information Technology Framework Risk Assessment And Management Diagrams PDF
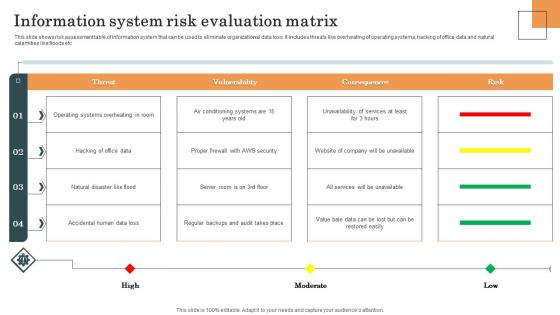
Information System Risk Evaluation Matrix Survey SS
This slide shows risk assessment table of information system that can be used to eliminate organizational data loss. It includes threats like overheating of operating systems, hacking of office data and natural calamities like floods etc. Showcasing this set of slides titled Information System Risk Evaluation Matrix Survey SS. The topics addressed in these templates are Information System, Risk Evaluation Matrix, Operating Systems. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Appvirality Capital Financing Elevator Pitch Deck Configuring And Scheduling Sample PDF
This slide shows that how the hack is being configured and scheduled in real time. The configuration timeline shows 3 steps which are page launch, growth hack and social actions and coupon configuration. Deliver and pitch your topic in the best possible manner with this Appvirality Capital Financing Elevator Pitch Deck Configuring And Scheduling Sample PDF Use them to share invaluable insights on Launching Page, Social Actions, Configuring Coupons and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Series Of Cyber Security Attacks Against Ukraine 2022 Threat Actors Supporting Russia And Ukraine Inspiration PDF
This slide shows the threat actors supporting russia and ukraine, such as hacker organization anonymous, cyber partisan hacking organization, and conti ransomware gang. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Series Of Cyber Security Attacks Against Ukraine 2022 Threat Actors Supporting Russia And Ukraine Inspiration PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
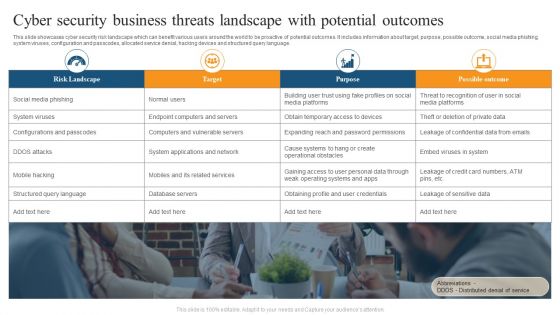
Cyber Security Business Threats Landscape With Potential Outcomes Ppt Outline Ideas PDF
This slide showcases cyber security risk landscape which can benefit various users around the world to be proactive of potential outcomes. It includes information about target, purpose, possible outcome, social media phishing, system viruses, configuration and passcodes, allocated service denial, hacking devices and structured query language. Persuade your audience using this Cyber Security Business Threats Landscape With Potential Outcomes Ppt Outline Ideas PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Risk Landscape, Target, Purpose, Possible Outcome. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
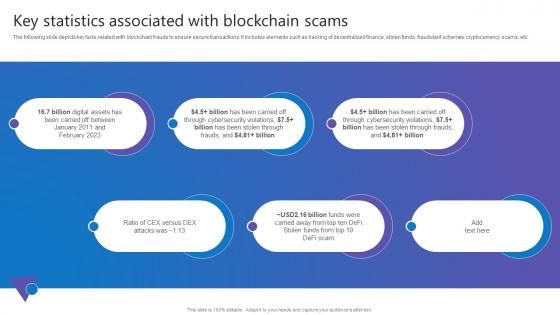
Key Statistics Associated Comprehensive Guide To Blockchain Digital Security Topics Pdf
The following slide depicts key facts related with blockchain frauds to ensure secure transactions. It includes elements such as hacking of decentralized finance, stolen funds, fraudulent schemes, cryptocurrency scams, etc. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Key Statistics Associated Comprehensive Guide To Blockchain Digital Security Topics Pdf and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Ukraine Cyberwarfare Cyber Attacks On Ukraine Are Conspicuous By Their Absence Topics Pdf
This slide represents the conspicuous Russian cyber attacks on Ukraine, including the attacks on government and banking websites, hacking of the countrys railway computer networks, etc. This is a ukraine cyberwarfare cyber attacks on ukraine are conspicuous by their absence topics pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like government and bank websites of ukraine were momentarily taken offline, team of anti war belarusian hackers claimed that the conflict had affected the countrys railways computer networks, hackers aided by ukraine launched distributed denial of service operations to take down russian websites. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
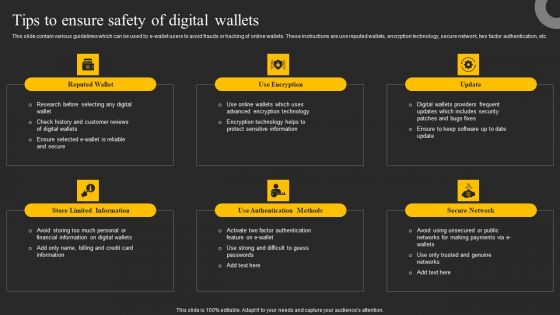
Tips To Ensure Safety Of Digital Wallets Ppt Summary Slide Download PDF
This slide contain various guidelines which can be used by e-wallet users to avoid frauds or hacking of online wallets. These instructions are use reputed wallets, encryption technology, secure network, two factor authentication, etc. Welcome to our selection of the Tips To Ensure Safety Of Digital Wallets Ppt Summary Slide Download PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi purpose template can be used in various situations. Grab these presentation templates today.

Wireless Banking To Improve Tips To Ensure Safety Of Digital Wallets Fin SS V
This slide contain various guidelines which can be used by e-wallet users to avoid frauds or hacking of online wallets. These instructions are use reputed wallets, encryption technology, secure network, two factor authentication, etc. The Wireless Banking To Improve Tips To Ensure Safety Of Digital Wallets Fin SS V is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
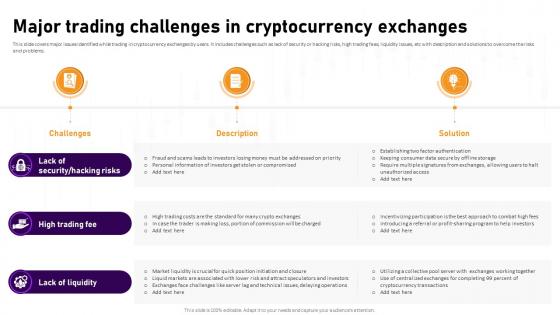
Major Trading Challenges In Cryptocurrency Exchanges Complete Roadmap To Blockchain BCT SS V
This slide covers major issues identified while trading in cryptocurrency exchanges by users. It includes challenges such as lack of security or hacking risks, high trading fees, liquidity issues, etc with description and solutions to overcome the risks and problems. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Major Trading Challenges In Cryptocurrency Exchanges Complete Roadmap To Blockchain BCT SS V for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
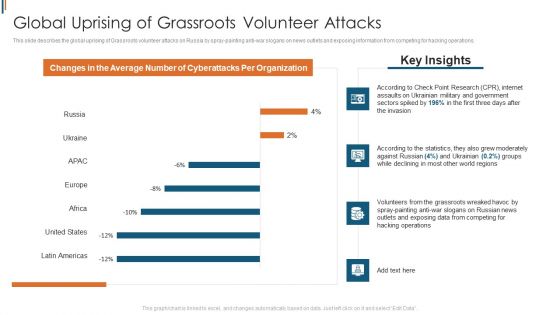
Ukraine Cyberwarfare Global Uprising Of Grassroots Volunteer Attacks Rules Pdf
This slide describes the global uprising of Grassroots volunteer attacks on Russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations. Deliver an awe inspiring pitch with this creative ukraine cyberwarfare global uprising of grassroots volunteer attacks rules pdf bundle. Topics like according to check point research cpr, internet assaults on ukrainian military, government sectors spiked by 196 percentage in the first three days after the invasion, according to the statistics, they also grew moderately against russian 4 percent, ukrainian 0.2 percent groups while declining in most other world regions can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

A Comprehensive Approach To Growth Competitive Analysis Of Growth Marketing MKT SS V
This slide illustrates the comparison between growth marketing and growth hacking that enable marketers to analyse both strategies. It compares them based on focus, approach, objective, methodology, planning, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give A Comprehensive Approach To Growth Competitive Analysis Of Growth Marketing MKT SS V a try. Our experts have put a lot of knowledge and effort into creating this impeccable A Comprehensive Approach To Growth Competitive Analysis Of Growth Marketing MKT SS V. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today

Overview Of Grey Hat Hackers Ppt Infographics Pictures PDF
This slide depicts the grey hat hackers and how they first hack any system, computer, software, or network and then ask for permission. This is a overview of grey hat hackers ppt infographics pictures pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like systems, security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Ukraine Cyberwarfare Ongoing Onslaught Of Russia On Ukraine Brochure Pdf
This slide represents the ongoing onslaught of Russia on Ukraine from December 2015 to Jan 2022. Russia has attacked Ukraine and other countries in many ways. Presenting ukraine cyberwarfare ongoing onslaught of russia on ukraine brochure pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like russian sponsored hack attacked microsoft exchange servers, hackers gained access to email accounts and networks worldwide, including in ukraine, the united states, and australia. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download

Signs For Various Digital Terrorism Attacks Brochure PDF
This slide shows various cyber terrorism attacks along with signs associated with each cyber attack. It include various cyber terrorism attacks such as Blackmailing Email Demand, Social Accounts Hacked etc. Presenting Signs For Various Digital Terrorism Attacks Brochure PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Attacked Network, Fraudulent Financial Transaction, Social Accounts Hacked. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Ukraine Cyberwarfare Facebook And Twitter Suggest Users In Ukraine Lock Their Accounts Information Pdf
This slide depicts Facebook and Twitters suggestion for Ukrainian citizens to close or lock their social media accounts as there are high chances of getting hacked in the hours of the war. Presenting ukraine cyberwarfare facebook and twitter suggest users in ukraine lock their accounts information pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like platforms urged users to be cautious about using the internet since they are in greater danger due to the war, in the hours following russias invasion of ukraine on thursday, social media sites hinted that users in the nation were more likely to have their accounts hacked. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
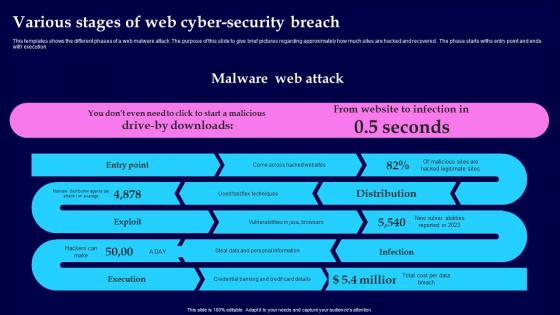
Various Stages Of Web Cyber Security Breach Introduction Pdf
This templates shows the different phases of a web malware attack. The purpose of this slide to give brief pictures regarding approximately how much sites are hacked and recovered. The phase starts withs entry point and ends with execution Pitch your topic with ease and precision using this Various Stages Of Web Cyber Security Breach Introduction Pdf This layout presents information on Malware Web Attack, Various Stages, Cyber Security Breach It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Five Steps For Cyber IT Security Risk Analysis Graphics PDF
This slide covers the steps for analysis of risk occurring in cyber security to reduce errors and system hacks so that the information of clients remain safe. It includes finding assets, identifying consequences, threats and assessing risk. Presenting Five Steps For Cyber IT Security Risk Analysis Graphics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Find Valuable Assets, Assess Risk, Identify Potential Consequences. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Russian Cyber Attacks On Ukraine IT Facebook And Twitter Suggest Rules PDF
This slide depicts Facebook and Twitters suggestion for Ukrainian citizens to close or lock their social media accounts as there are high chances of getting hacked in the hours of the war. This is a russian cyber attacks on ukraine it facebook and twitter suggest rules pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like social media, accounts, strategy, security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Data Wiper Spyware Attack Facebook And Twitter Suggest Users In Ukraine Lock Their Accounts Clipart PDF
This slide depicts Facebook and Twitters suggestion for Ukrainian citizens to close or lock their social media accounts as there are high chances of getting hacked in the hours of the war.Deliver and pitch your topic in the best possible manner with this data wiper spyware attack facebook and twitter suggest users in ukraine lock their accounts clipart pdf Use them to share invaluable insights on disseminate disinformation, included everything, prematurely canceling and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Techniques To Monitor Transactions Real Time Atm Fraud And Crime Detection Slides PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Take your projects to the next level with our ultimate collection of Techniques To Monitor Transactions Real Time Atm Fraud And Crime Detection Slides PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors theyll make your projects stand out from the rest.
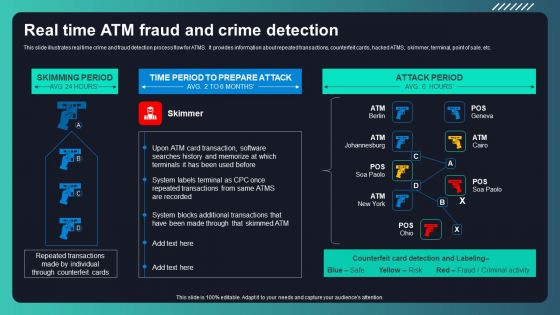
Deploying AML Transaction Monitoring Real Time ATM Fraud And Crime Detection Designs PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Boost your pitch with our creative Deploying AML Transaction Monitoring Real Time ATM Fraud And Crime Detection Designs PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
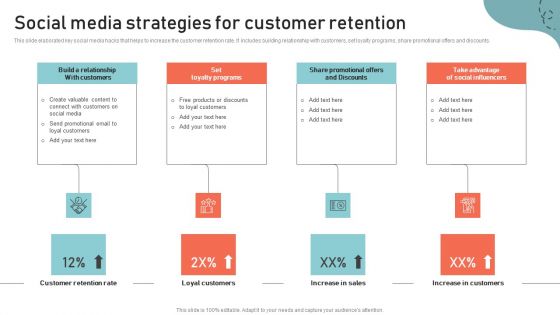
Optimizing Multichannel Strategy To Improve User Experience Social Media Strategies Ideas PDF
This slide elaborated key social media hacks that helps to increase the customer retention rate. It includes building relationship with customers, set loyalty programs, share promotional offers and discounts. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Optimizing Multichannel Strategy To Improve User Experience Social Media Strategies Ideas PDF from Slidegeeks and deliver a wonderful presentation.
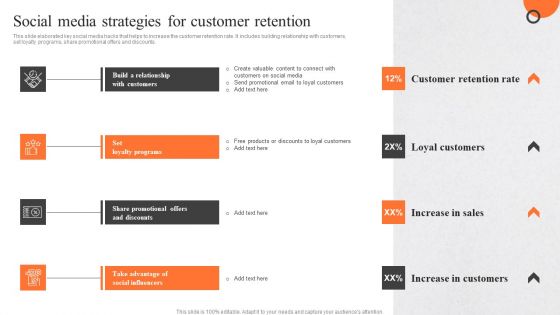
Enhancing Buyer Journey Social Media Strategies For Customer Retention Mockup PDF

Client Feedback Strategies Social Media Strategies For Customer Retention Infographics Pdf
This slide elaborated key social media hacks that helps to increase the customer retention rate. It includes building relationship with customers, set loyalty programs, share promotional offers and discounts. Find a pre designed and impeccable Client Feedback Strategies Social Media Strategies For Customer Retention Infographics Pdf. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

KYC Transaction Monitoring System Business Security Real Time Atm Fraud And Crime Detection Themes PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give KYC Transaction Monitoring System Business Security Real Time Atm Fraud And Crime Detection Themes PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable KYC Transaction Monitoring System Business Security Real Time Atm Fraud And Crime Detection Themes PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.

Series Of Cyber Security Attacks Against Ukraine 2022 Facebook And Twitter Suggest Users In Ukraine Lock Their Accounts Professional PDF
This slide depicts facebook and twitters suggestion for ukrainian citizens to close or lock their social media accounts as there are high chances of getting hacked in the hours of the war. Present like a pro with Series Of Cyber Security Attacks Against Ukraine 2022 Facebook And Twitter Suggest Users In Ukraine Lock Their Accounts Professional PDF Create beautiful presentations together with your team, using our easy to use presentation slides. Share your ideas in real time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
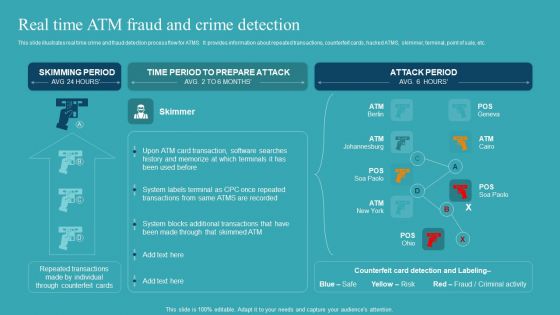
Integrating AML And Transaction Real Time ATM Fraud And Crime Detection Introduction PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Integrating AML And Transaction Real Time ATM Fraud And Crime Detection Introduction PDF to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Integrating AML And Transaction Real Time ATM Fraud And Crime Detection Introduction PDF.

Enhancing CX Strategy Social Media Strategies For Customer Retention Pictures PDF
This slide elaborated key social media hacks that helps to increase the customer retention rate. It includes building relationship with customers, set loyalty programs, share promotional offers and discounts. Retrieve professionally designed Enhancing CX Strategy Social Media Strategies For Customer Retention Pictures PDF to effectively convey your message and captivate your listeners. Save time by selecting pre made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
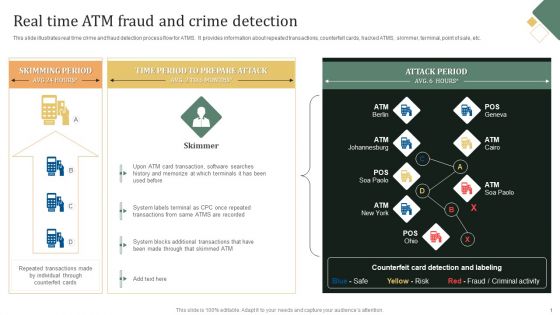
Transaction Monitoring Real Time ATM Fraud And Crime Detection Infographics PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Transaction Monitoring Real Time ATM Fraud And Crime Detection Infographics PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Transaction Monitoring Real Time ATM Fraud And Crime Detection Infographics PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
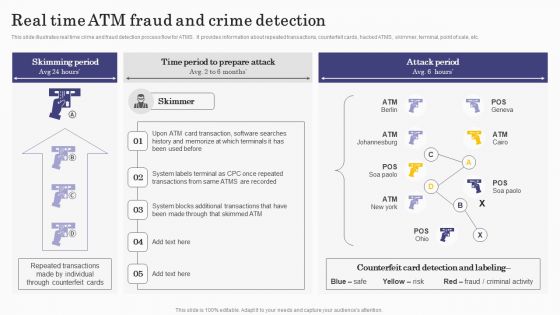
Deploying Banking Transaction Real Time Atm Fraud And Crime Detection Download PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Retrieve professionally designed Deploying Banking Transaction Real Time Atm Fraud And Crime Detection Download PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You dont have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
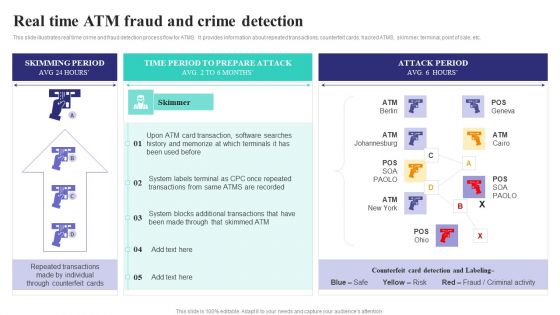
Formulating Money Laundering Real Time Atm Fraud And Crime Detection Brochure PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Slidegeeks has constructed Table Of Contents For Formulating Money Laundering Real Time Atm Fraud And Crime Detection Brochure PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

Actual Time Transaction Monitoring Software And Strategies Real Time ATM Fraud And Crime Detection Elements PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Retrieve professionally designed Actual Time Transaction Monitoring Software And Strategies Real Time ATM Fraud And Crime Detection Elements PDF to effectively convey your message and captivate your listeners. Save time by selecting pre made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
Creating Transaction Monitoring Real Time ATM Fraud And Crime Detection Icons PDF
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Slidegeeks has constructed Creating Transaction Monitoring Real Time ATM Fraud And Crime Detection Icons PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

Customer Experience Optimization Social Media Strategies For Customer Retention Pictures PDF
This slide elaborated key social media hacks that helps to increase the customer retention rate. It includes building relationship with customers, set loyalty programs, share promotional offers and discounts. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Customer Experience Optimization Social Media Strategies For Customer Retention Pictures PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Customer Experience Optimization Social Media Strategies For Customer Retention Pictures PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
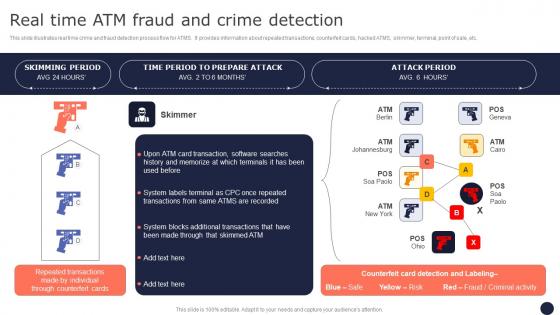
Real Time ATM Fraud And Crime Detection Mitigating Corporate Scams And Robberies Pictures Pdf
This slide illustrates real time crime and fraud detection process flow for ATMS. It provides information about repeated transactions, counterfeit cards, hacked ATMS, skimmer, terminal, point of sale, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Real Time ATM Fraud And Crime Detection Mitigating Corporate Scams And Robberies Pictures Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Real Time ATM Fraud And Crime Detection Mitigating Corporate Scams And Robberies Pictures Pdf.
Business And Threats Landscape In Business Cybersecurity Ppt Icon Example Introduction PDF
This slide showcases risk and threats landscape which can be referred by businesses to be aware of cybersecurity issues and attacks. It contains information about phishing, malware and blackmail hacking. Presenting Business And Threats Landscape In Business Cybersecurity Ppt Icon Example Introduction PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Phishing, Malware, Blackmail Hacking. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Client Acquisition Strategic Plan Activities In Marketing Microsoft Pdf
This slide presents B2B lead generation activities used by brands in marketing that helps them to generate business opportunities further utilized by sales team to convert potential customers into buyers. It includes growth hacking, content marketing and account based marketing. Showcasing this set of slides titled Client Acquisition Strategic Plan Activities In Marketing Microsoft Pdf. The topics addressed in these templates are Growth Hacking, Account Based Marketing, Content Marketing. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
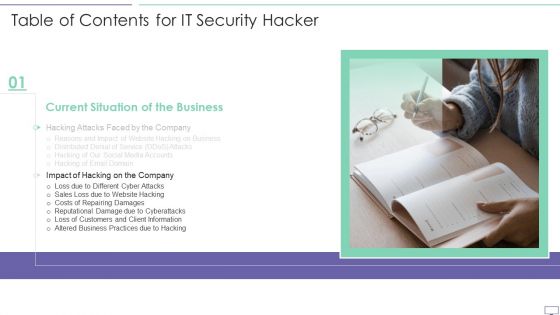
Table Of Contents For IT Security Hacker Slide Introduction PDF
Deliver an awe inspiring pitch with this creative Table Of Contents For IT Security Hacker Slide Introduction PDF bundle. Topics like Prevent Hacking, Strategies On Business, Implementation Plan can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Table Of Contents For Cyber Exploitation IT Pictures PDF
Deliver an awe inspiring pitch with this creative table of contents for cyber exploitation it pictures pdf bundle. Topics like budget, implementation plan, strategies to prevent hacking, impact of new strategies on business, current situation of the business can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
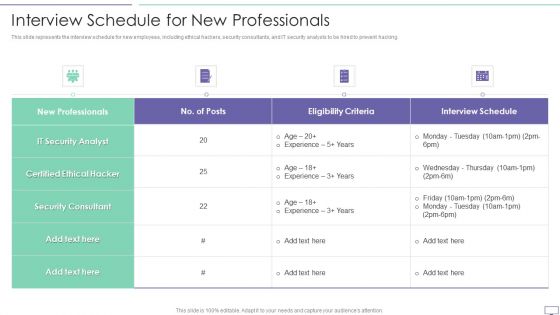
IT Security Hacker Interview Schedule For New Professionals Portrait PDF
This slide represents the interview schedule for new employees, including ethical hackers, security consultants, and IT security analysts to be hired to prevent hacking.Deliver and pitch your topic in the best possible manner with this IT Security Hacker Interview Schedule For New Professionals Portrait PDF. Use them to share invaluable insights on Ethical Hacker, Security Consultant, Security Analyst and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Table Of Contents For IT Security Hacker Background PDF
This is a Table Of Contents For IT Security Hacker Background PDF template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Current Situation, Impact Of Hacking, Repairing Damages. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Cyber Exploitation IT Interview Schedule For New Professionals Icons PDF
This slide represents the interview schedule for new employees, including ethical hackers, security consultants, and IT security analysts to be hired to prevent hacking. Deliver and pitch your topic in the best possible manner with this cyber exploitation it interview schedule for new professionals icons pdf. Use them to share invaluable insights on it security analyst, certified ethical hacker, security consultant and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Online Security Learning System For Malware Threat Control Ppt PowerPoint Presentation Layouts Portfolio PDF
Presenting this set of slides with name online security learning system for malware threat control ppt powerpoint presentation layouts portfolio pdf. This is a three stage process. The stages in this process are network protection and control, access control protection, email and web browser protections, virus penetration testing and control fundamentals, password protection, wireless protection, cyber incitement management, ethical hacking. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Internet Security Threat Analysis With Attacks Target And Purpose Ppt PowerPoint Presentation Pictures Structure PDF
Presenting internet security threat analysis with attacks target and purpose ppt powerpoint presentation pictures structure pdf to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including social and phishing, passwords and configs, smart and mobile hacking. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Major Social Media Protection And Privacy Issues Template PDF
The following slide highlights some social media security threats to safeguard unauthorized access. It includes elements such as data mining, hacking, harassment, cyberbullying, privacy loophole etc. Presenting Major Social Media Protection And Privacy Issues Template PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Data Mining, Harassment And Cyberbullying, Privacy Loophole. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

AI And ML Driving Monetary Value For Organization Required Manpower Skills Set Visualization Rules PDF
Following slide shows details about required manpower skills set. Skills set covered are domain knowledge, machine learning, data visualization and hacking. Deliver an awe inspiring pitch with this creative ai and ml driving monetary value for organization required manpower skills set visualization rules pdf bundle. Topics like domain knowledge, machine learning, machine learning, data visualization can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
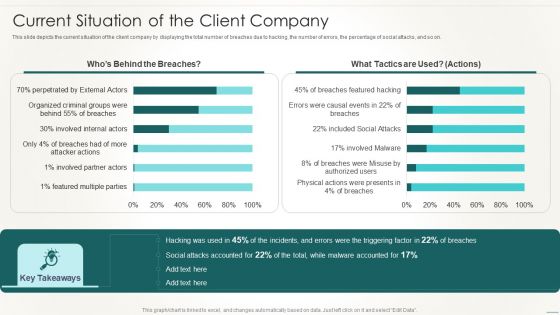
Information Technology Disaster Resilience Plan Current Situation Of The Client Company Designs PDF
This slide depicts the current situation of the client company by displaying the total number of breaches due to hacking, the number of errors, the percentage of social attacks, and so on.Deliver an awe inspiring pitch with this creative Information Technology Disaster Resilience Plan Current Situation Of The Client Company Designs PDF bundle. Topics like Disaster Recovery, Facilities Management, Collaboration can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
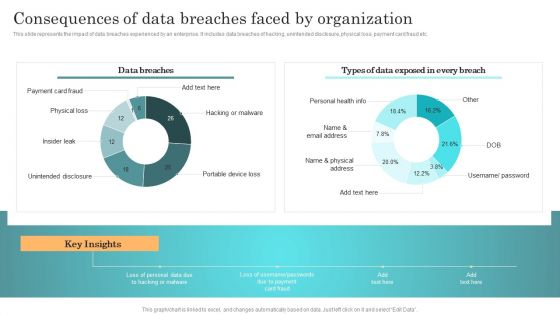
Incident Response Techniques Deployement Consequences Of Data Breaches Faced By Organization Structure PDF
This slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. There are so many reasons you need a Incident Response Techniques Deployement Consequences Of Data Breaches Faced By Organization Structure PDF. The first reason is you cannot spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

IT Security Hacker Ethical Hacker And Why We Need Ethical Hacker Guidelines PDF
This slide depicts the reasons to describe the need for ethical hacking, including identification and correction of security flaws, aid in development quality control, and evaluation of the companys security regulatory compliance.Presenting IT Security Hacker Ethical Hacker And Why We Need Ethical Hacker Guidelines PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Systems, Applications, Correcting Security, Regulatory Compliance. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Cyber Exploitation IT Ethical Hacker And Why We Need Ethical Hacker Information PDF
This slide depicts the reasons to describe the need for ethical hacking, including identification and correction of security flaws, aid in development and quality control, and evaluation of the companys security and regulatory compliance. This is a cyber exploitation it ethical hacker and why we need ethical hacker information pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like security flaws, development and quality control, evaluate security and regulatory compliance. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Smart Home System Security Threats Utilizing Smart Appliances IoT SS V
This slide provides an overview of the threats to smart house systems and their solution. Major threats covered are device hacking, distributed denial of service, data and identity theft. Take your projects to the next level with our ultimate collection of Smart Home System Security Threats Utilizing Smart Appliances IoT SS V. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest

Data Security And Privacy Audit Questionnaire Overview Report Survey SS
Following slides demonstrates data security evaluation summary report which can be used by business to reduce data hacking. It includes elements such as data security tools, budget allocation on tools, satisfaction level with tools, etc. Pitch your topic with ease and precision using this Data Security And Privacy Audit Questionnaire Overview Report Survey SS. This layout presents information on Data Security Tools, Budget Allocated, Tools Performance, Data Security Tools Management. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Online Security Threat And Risk Assessment Matrix Formats PDF
This slide showcases digital safety risk assessment matrix which helps analyze impact of threat on business processes. It provides information regarding hacking, data breaches, information misuse, malicious attacks and system failure. Showcasing this set of slides titled Online Security Threat And Risk Assessment Matrix Formats PDF. The topics addressed in these templates are Information Misuse, Data Breaches, Malicious Attacks. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
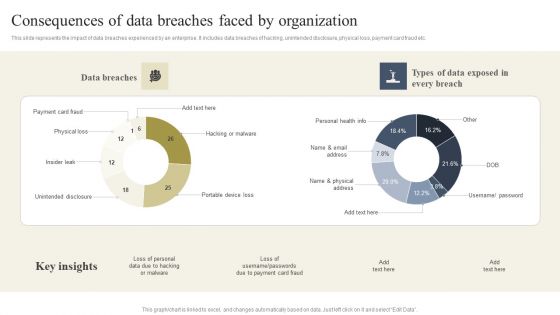
Cyber Security Breache Response Strategy Consequences Of Data Breaches Faced By Organization Elements PDF
This slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Boost your pitch with our creative Cyber Security Breache Response Strategy Consequences Of Data Breaches Faced By Organization Elements PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
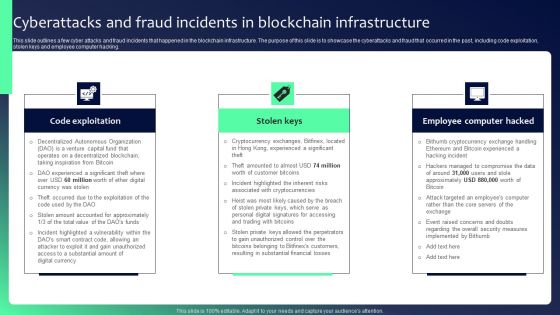
Blockchain Security Solutions Deployment Cyberattacks And Fraud Incidents In Blockchain Clipart PDF
This slide outlines a few cyber attacks and fraud incidents that happened in the blockchain infrastructure. The purpose of this slide is to showcase the cyberattacks and fraud that occurred in the past, including code exploitation, stolen keys and employee computer hacking. There are so many reasons you need a Blockchain Security Solutions Deployment Cyberattacks And Fraud Incidents In Blockchain Clipart PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

 Home
Home